Discover Cybersecurity Tech Brief By HackerNoon
Cybersecurity Tech Brief By HackerNoon

323 Episodes
Reverse
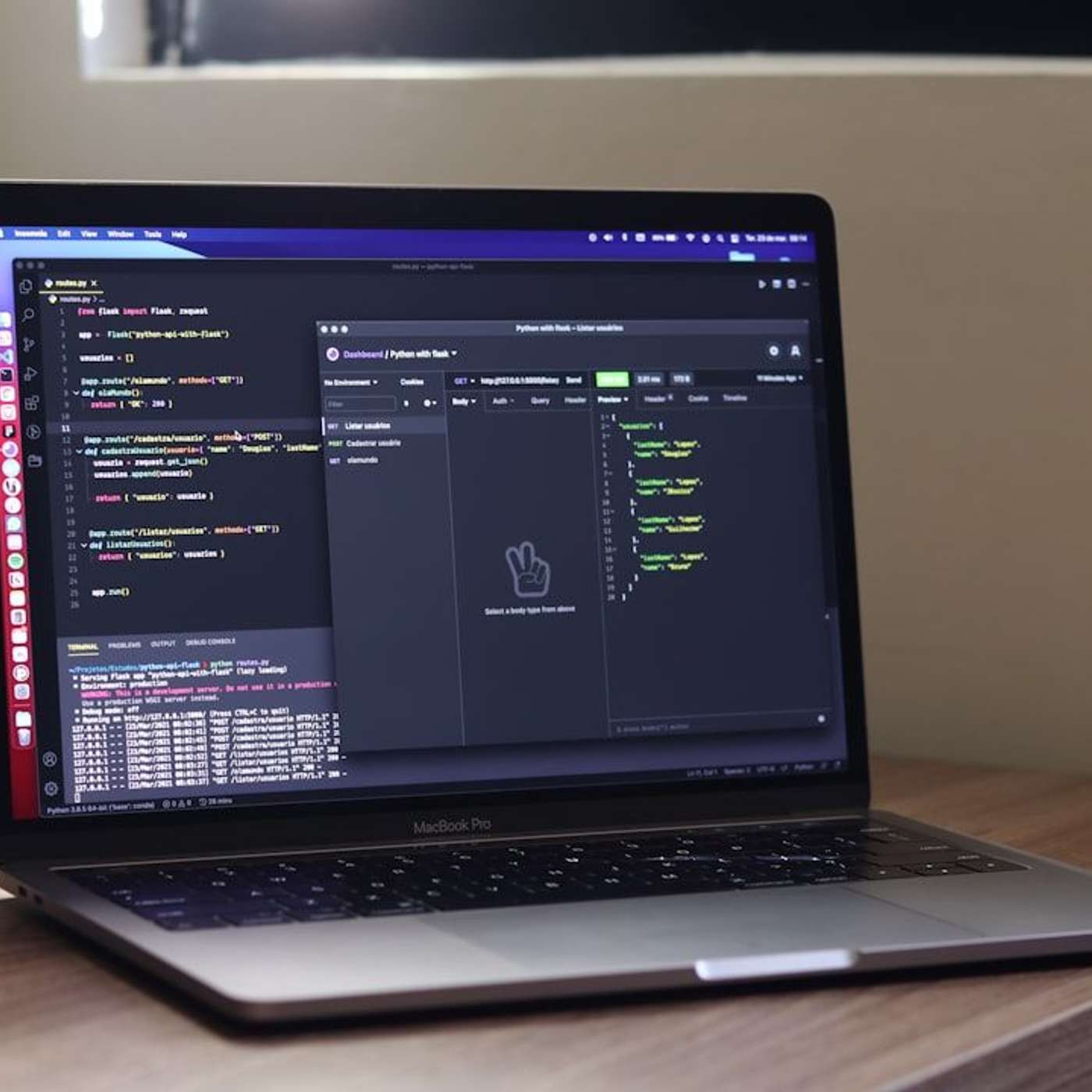
This story was originally published on HackerNoon at: https://hackernoon.com/the-secure-force-building-an-end-to-end-sdlc-without-breaking-the-bank.
Secure your SDLC without breaking the bank. Learn phase-wise security practices and open-source tools nonprofits can use to build safer, resilient software.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cyber-security, #open-source, #nonprofits, #sdlc-phases, #secure-software-development, #end-to-end-sdlc, #sdlc, #software-development, and more.
This story was written by: @atishkdash. Learn more about this writer by checking @atishkdash's about page,
and for more stories, please visit hackernoon.com.
Stop treating security as an afterthought. Learn how to integrate it into every phase of the SDLC—requirements, design, development, testing, deployment, and maintenance—using practical, low-cost open-source tools to build safer, more resilient software.
This story was originally published on HackerNoon at: https://hackernoon.com/the-myth-of-unhackable-biometrics-and-what-attackers-actually-try.
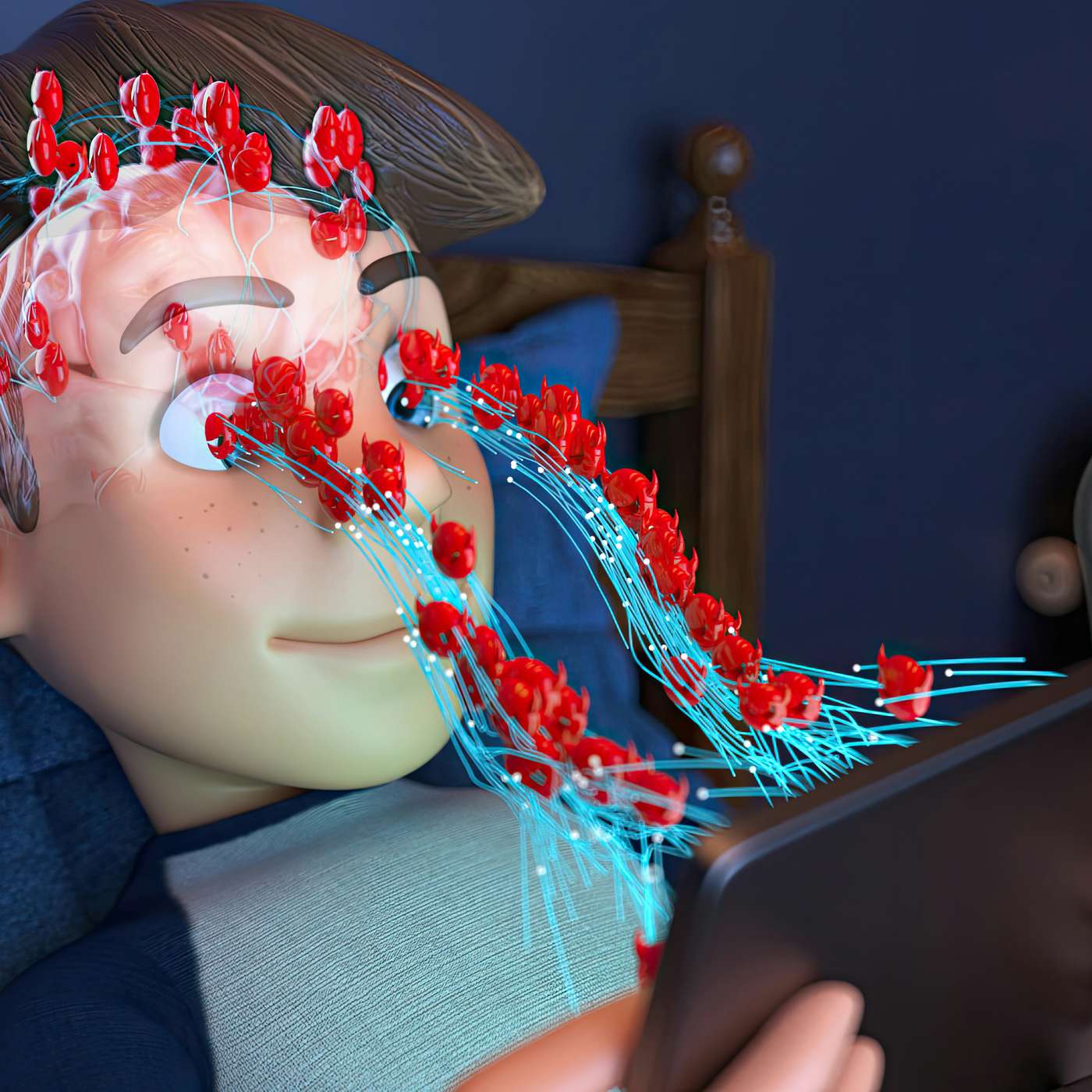
Biometrics feel unhackable—until you learn how spoofing works.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #biometrics, #authentication, #privacy, #infosec, #security-research, #biometric-spoofing, #face-id-spoofing, and more.
This story was written by: @cybersafetyzone386. Learn more about this writer by checking @cybersafetyzone386's about page,
and for more stories, please visit hackernoon.com.
Biometric authentication isn’t unhackable. Researchers continue to find ways to spoof Face ID and fingerprint systems, but real-world attacks usually combine technical tricks with social engineering. Biometrics remain effective when used as part of layered security — not as a standalone defense.
This story was originally published on HackerNoon at: https://hackernoon.com/securing-the-digital-nerve-system-a-practical-guide-to-implementing-zero-trust-api-security.
Learn how Zero Trust secures APIs, prevents breaches, and ensures every request is verified in modern microservices and cloud environments.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #zero-trust-security, #cybersecurity, #cloud-computing, #devsecops, #cyber-security, #microservices, #oauth2, #mtls, and more.
This story was written by: @atishkdash. Learn more about this writer by checking @atishkdash's about page,
and for more stories, please visit hackernoon.com.
APIs are the backbone of modern enterprises, connecting services, data, and business logic across microservices and cloud environments. Traditional perimeter-based security is no longer enough, as remote work, cloud adoption, and constant machine-to-machine communication blur internal and external boundaries. Zero Trust shifts the security model from “trust but verify” to “never trust, always verify,” treating every API request as potentially malicious. By enforcing strong identity verification through OAuth2, OpenID Connect, and mTLS, and applying granular authorization with attribute-based access control and JWT scopes, organizations can ensure that only the right entities access the right resources. API gateways and policy enforcement points provide centralized control, logging, and rate-limiting, while micro-segmentation and continuous inspection prevent lateral movement and detect anomalies in real time. Implementing Zero Trust requires collaboration across development, security, and operations teams but results in resilient, secure APIs that protect sensitive data, limit risk, and enable business agility.
This story was originally published on HackerNoon at: https://hackernoon.com/one-identity-appoints-gihan-munasinghe-as-chief-technology-officer.
He specializes in scaling global engineering teams and modernizing complex legacy platforms to drive product innovation. “This is a pivotal moment for One Ident
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #cybernewswire, #press-release, #cyber-security-awareness, #cybercrime, #cybersecurity-awareness, #cyber-attack, #good-company, and more.
This story was written by: @cybernewswire. Learn more about this writer by checking @cybernewswire's about page,
and for more stories, please visit hackernoon.com.
Gihan Munasinghe brings more than 15 years of experience leading global engineering organizations and delivering large-scale, customer-centric software platforms. He specializes in scaling global engineering teams and modernizing complex legacy platforms to drive product innovation. “This is a pivotal moment for One Identity and the identity security industry,” said Munasing he.
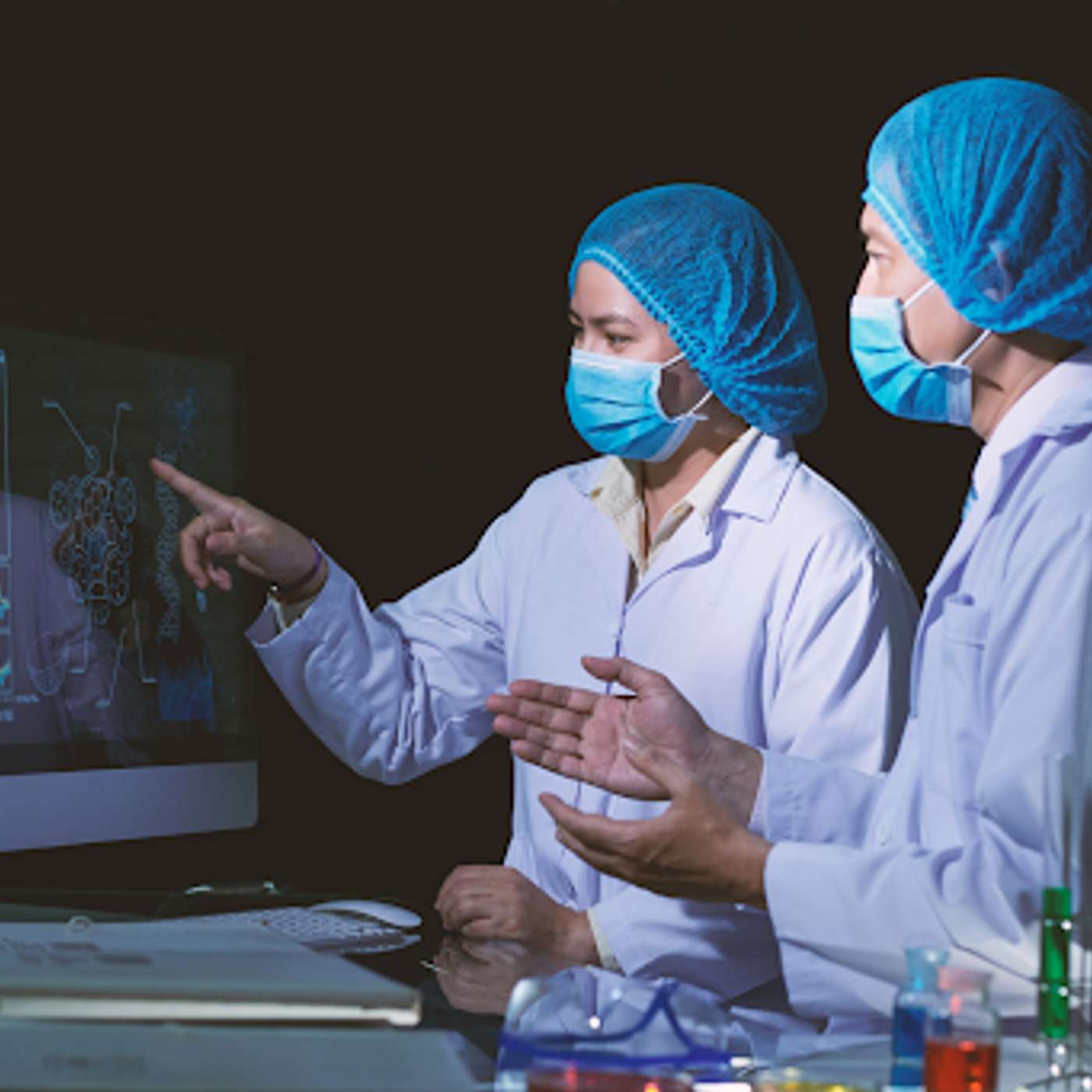
This story was originally published on HackerNoon at: https://hackernoon.com/the-next-generation-of-cybersecurity-protection-for-healthcare.
Mohammed Nayeem pioneers AI-driven cybersecurity and hospital-specific frameworks, protecting clinical systems, devices, and patient lives worldwide.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #healthcare-cybersecurity, #ai-anomaly-detection-hospitals, #clinical-it-security-framework, #patient-safety-cybersecurity, #hybrid-data-corruption-attacks, #predictive-hospital-security, #medical-device-security, #good-company, and more.
This story was written by: @jonstojanjournalist. Learn more about this writer by checking @jonstojanjournalist's about page,
and for more stories, please visit hackernoon.com.
Mohammed Nayeem transforms healthcare cybersecurity, developing AI anomaly detection platforms and hospital-specific security frameworks that reduce response times from hours to minutes, secure medical devices, and protect patient data. His proactive approach integrates security into clinical workflows, preventing ransomware, hybrid data attacks, and operational shutdowns while safeguarding patient safety at scale.
This story was originally published on HackerNoon at: https://hackernoon.com/the-ai-arms-race-offense-vs-defense.
Welcome to the AI arms race. It's been happening for years, and the data confirms what security professionals feared: most organizations are on the losing side.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #artificial-intelligence, #ai-security, #ai-defense, #ai-arms-race, #ai-security-awareness, #ai-cyber-security, #ai-cyber-threats, and more.
This story was written by: @anjaligopinadhan. Learn more about this writer by checking @anjaligopinadhan's about page,
and for more stories, please visit hackernoon.com.
Check Point's Cyber Security Report 2026 shows 70% increase in cyber attacks since 2023. 60% of executives reported their organizations faced AI-powered attacks, but only 7% had deployed AI defenses at scale. Moody's 2026 cyber outlook warns that AI-related threats will "become more prevalent and pronounced"
This story was originally published on HackerNoon at: https://hackernoon.com/keycloak-client-aware-access-control.
Keycloak's realm model allows any user in a realm to authenticate any registered client.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #keycloak, #keycloak-authentication, #aware-access-control, #opensource-identity-management, #access-management-solution, #access-management, #authentication, and more.
This story was written by: @erindeji. Learn more about this writer by checking @erindeji's about page,
and for more stories, please visit hackernoon.com.
Keycloak's realm model allows any user in a realm to authenticate any registered client.
This story was originally published on HackerNoon at: https://hackernoon.com/how-genai-security-engineer-chetan-pathade-is-protecting-the-next-era-of-ai.
Chetan Pathade, GenAI Security Engineer, protects AI systems from adversarial attacks, data leaks, and cloud vulnerabilities at enterprise scale.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #genai-security-engineer, #llm-model-protection, #cloud-security-ai-2026, #adversarial-ai-threats, #prompt-injection-defense, #cybersecurity-leadership-ai, #chetan-pathade-aws-security, #good-company, and more.
This story was written by: @jonstojanjournalist. Learn more about this writer by checking @jonstojanjournalist's about page,
and for more stories, please visit hackernoon.com.
Chetan Pathade, a GenAI Security Engineer at AWS, secures AI systems and cloud infrastructure against data leaks, adversarial attacks, and emerging cyber threats. From bug bounty beginnings to advanced LLM protection, Pathade blends practical skill, academic rigor, and continuous learning to safeguard enterprises while preparing the next generation of cybersecurity talent.
This story was originally published on HackerNoon at: https://hackernoon.com/why-ephemerality-is-a-stronger-privacy-primitive-than-encryption-alone.
Why ephemerality beats encryption alone for privacy: a technical deep dive into data lifecycles, threat models, and modern privacy-preserving architectures.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #privacy, #security, #browsers, #encryption, #ephemerality, #privacy-primitive, #digital-privacy, and more.
This story was written by: @akshat666. Learn more about this writer by checking @akshat666's about page,
and for more stories, please visit hackernoon.com.
Why ephemerality beats encryption alone for privacy: a technical deep dive into data lifecycles, threat models, and modern privacy-preserving architectures.
This story was originally published on HackerNoon at: https://hackernoon.com/outlook-vs-gmail-choosing-the-kind-of-email-security-your-business-can-live-with.
Outlook and Gmail are both secure, but built differently. See how control, compliance, and risk management compare for business email in 2025.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #email-security, #it-security, #outlook-vs-gmail-security, #business-email-security, #outlook-vs-gmail-for-business, #microsoft-365-security, #google-workspace-security, #secure-business-email, and more.
This story was written by: @oladapo1. Learn more about this writer by checking @oladapo1's about page,
and for more stories, please visit hackernoon.com.
Both Outlook and Gmail offer strong business email security in 2025, but Outlook favors granular control and compliance, while Gmail prioritizes simplicity and low-maintenance protection.
This story was originally published on HackerNoon at: https://hackernoon.com/beyond-smartphones-motorolas-pivot-to-iot-security-and-smart-home-surveillance.
Examine Motorola’s pivot to IoT security and smart home surveillance. We highlight key features and infrastructure to decode what's important in home safety.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #iot-security, #iot-applications, #mobile, #mobile-app-development, #cybersecurity, #cybercrime, #cyber-threats, #smart-home-surveillance, and more.
This story was written by: @ASmith. Learn more about this writer by checking @ASmith's about page,
and for more stories, please visit hackernoon.com.
Examine Motorola’s pivot to IoT security and smart home surveillance. We highlight key features and infrastructure to decode what's important in home safety.
This story was originally published on HackerNoon at: https://hackernoon.com/the-ddos-of-human-attention-why-curl-killed-its-bug-bounty-and-what-it-means-for-devops.
AI-gen "slop" is killing bug bounties. Learn why cURL shut down its program and how to protect your team from the new DDoS: the flood of low-quality AI noise.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #ai-slop, #devops, #open-source, #bug-bounty, #ddos-of-human-attention, #curl, #command-line-tool, and more.
This story was written by: @omotayojude. Learn more about this writer by checking @omotayojude's about page,
and for more stories, please visit hackernoon.com.
AI-gen "slop" is killing bug bounties. Learn why cURL shut down its program and how to protect your team from the new DDoS: the flood of low-quality AI noise.
This story was originally published on HackerNoon at: https://hackernoon.com/zero-trust-security-in-2026-a-complete-implementation-roadmap-for-ctos.
Zero Trust Security focuses on not believing on any user, any device or anyone even if they are in your network perimeter.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #roadmap, #zero-trust-security, #cto, #2026, #software-development, #zero-trust-security-in-2026, #good-company, and more.
This story was written by: @mahipal.nehra. Learn more about this writer by checking @mahipal.nehra's about page,
and for more stories, please visit hackernoon.com.
Zero Trust Security focuses on not believing on any user, any device or anyone even if they are in your network perimeter. As AI systems become deeply embedded into business workflows, organizations must rethink how they protect sensitive data and automated decision pipelines.
This story was originally published on HackerNoon at: https://hackernoon.com/understanding-testing-vs-evaluation-in-ai-systems.
The distinction between testing and evaluation in AI systems
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #ai-security, #ai-agent, #ai-systems, #ai-red-teaming, #artificial-intelligence, #testing-ai-systems, #security-testing, #best-testing-practices, and more.
This story was written by: @lab42ai. Learn more about this writer by checking @lab42ai's about page,
and for more stories, please visit hackernoon.com.
AI systems introduce complexity: behaviors emerge from training rather than explicit programming. Many companies and organizations building AI systems, especially AI agents, run into problems. They focus heavily on evaluations while neglecting systematic testing.
This story was originally published on HackerNoon at: https://hackernoon.com/owasp-top-10-the-security-stuff-you-keep-meaning-to-learn.
A practical, plain-English guide to the OWASP Top 10—what they mean, how they show up in real apps, and where to start fixing them.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #web-security, #owasp, #owasp-top-10, #broken-access-control, #security-misconfiguration, #server-side-request-forgery, #injection-attacks, #insecure-application-design, and more.
This story was written by: @anjali002. Learn more about this writer by checking @anjali002's about page,
and for more stories, please visit hackernoon.com.
OWASP is a nonprofit that publishes a Top 10 list of security breaches. The list reflects what's actually hurting organizations right now. Broken access control is at the top for a reason. Insecure design is the problem.
This story was originally published on HackerNoon at: https://hackernoon.com/a-class-for-mom-part-2-cybersecurity.
This is a cybersecurity class for senior citizens.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #education, #senior-wisdom, #learning, #online-learning, and more.
This story was written by: @turbulence. Learn more about this writer by checking @turbulence's about page,
and for more stories, please visit hackernoon.com.
This is a cybersecurity class for senior citizens.
This story was originally published on HackerNoon at: https://hackernoon.com/inside-brevity-ai-the-architecture-powering-real-time-hipaa-compliant-clinical-documentation.
Brevity AI’s CTO architected a HIPAA-compliant platform using real-time AI to transform clinical documentation and visit prep at scale.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #hipaa-compliant-documentation, #healthcare-ai-system, #healthcare-nlp-clinical-notes, #secure-healthcare-data, #medical-documentation, #healthcare-ai-architecture, #medical-transcription-platform, #good-company, and more.
This story was written by: @sanya_kapoor. Learn more about this writer by checking @sanya_kapoor's about page,
and for more stories, please visit hackernoon.com.
Brevity AI’s clinical documentation platform compresses hours of chart review and note-taking into minutes through real-time, HIPAA-compliant AI. Architected end-to-end by CTO Purv Rakeshkumar Chauhan, the system combines scalable microservices, medical NLP, secure data infrastructure, and real-time transcription to improve clinician efficiency, accuracy, and patient care.
This story was originally published on HackerNoon at: https://hackernoon.com/how-you-can-test-your-kids-smart-toys-for-privacy.
Are those toys secure? And precisely what data is being handed over when a kid is using these toys?
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #privacy, #kids-safety, #children-privacy, #children-data-safety, #kids-toys-privacy, #the-markup, #bluetooth-toys, #hackernoon-top-story, and more.
This story was written by: @TheMarkup. Learn more about this writer by checking @TheMarkup's about page,
and for more stories, please visit hackernoon.com.
The Markup is looking into what other toys collect private data on your children. A Wi-Fi-enabled toy will likely communicate with your wireless router. A Bluetooth toy will send data to another smart device, such as a smartphone. We’re here to help.
This story was originally published on HackerNoon at: https://hackernoon.com/new-research-shows-64percent-of-third-party-applications-access-sensitive-data-without-authorization.
64% of third‑party applications access sensitive data without legitimate business justification. Google Tag Manager (8%), Shopify (5%), and Facebook Pixel (4%)
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity, #reflectiz, #cybernewswire, #press-release, #cyber-threats, #cyber-security-awareness, #cybersecurity-tips, #good-company, and more.
This story was written by: @cybernewswire. Learn more about this writer by checking @cybernewswire's about page,
and for more stories, please visit hackernoon.com.
Reflectiz releases its 2026 State of Web Exposure Research. 64% of third‑party applications access sensitive data without legitimate business justification. Google Tag Manager (8%), Shopify (5%), and Facebook Pixel (4%) are top drivers of sensitive data exposure.
This story was originally published on HackerNoon at: https://hackernoon.com/essential-cybersecurity-measures-every-modern-business-should-take.
No business can remove all cyber risk, but every business can make smart moves that reduce it.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #cybersecurity-tips, #business-intelligence, #cyber-threats, #cyber-security-awareness, #cyber-attack, #cybersecurity, #essential-cybersecurity, #startup, and more.
This story was written by: @setudeora. Learn more about this writer by checking @setudeora's about page,
and for more stories, please visit hackernoon.com.
No business can remove all cyber risk, but every business can make smart moves that reduce it.