Discover Entra.Chat
Entra.Chat

Entra.Chat
Author: Merill Fernando
Subscribed: 15Played: 986Subscribe
Share
© Merill & Joshua Fernando
Description
Entra Chat is a weekly podcast hosted by Merill Fernando and delivers practical insights for Microsoft administrators and security professionals through conversations with identity experts who've been in the trenches.
Episodes feature seasoned Entra practitioners sharing real-world deployment experiences and Microsoft Entra team members who build the features you use daily.
Get the inside track on best practices, implementation strategies, and upcoming capabilities directly from those who design and deploy Microsoft identity solutions.
Join us for actionable takeaways you can apply immediately in your Microsoft 365, Azure, and Entra environments.
---
Entra.Chat, its content and opinions are my (Merill Fernando) own and do not reflect the views of my employer (Microsoft). All postings are provided “AS IS” with no warranties and is not supported by the author. All trademarks and copyrights belong to their owners and are used for identification only.
entra.news
Episodes feature seasoned Entra practitioners sharing real-world deployment experiences and Microsoft Entra team members who build the features you use daily.
Get the inside track on best practices, implementation strategies, and upcoming capabilities directly from those who design and deploy Microsoft identity solutions.
Join us for actionable takeaways you can apply immediately in your Microsoft 365, Azure, and Entra environments.
---
Entra.Chat, its content and opinions are my (Merill Fernando) own and do not reflect the views of my employer (Microsoft). All postings are provided “AS IS” with no warranties and is not supported by the author. All trademarks and copyrights belong to their owners and are used for identification only.
entra.news
55 Episodes
Reverse
Microsoft just dropped a massive wave of features for Entra, and the rules of Tenant Governance have officially changed. Join us as we talk to three world-class MVPs about their hands-on experience with the new Entra Backup and Recovery and Tenant Governance features.Our Microsoft MVP guests Nathan McNulty, Ru Campbell, and Thomas Naunheim break down the most exciting new features in Microsoft Entra.In this episode, we explore:* The “Shadow Tenant” Problem: One org found 700+ Entra tenants they didn’t know they had.* Version Control for Admins: Why “Difference Reports” are a total game-changer for troubleshooting.* Recovery Safeguards: How to protect your tenant from accidental deletions and “sneaky” background changes.* Backup & Recovery: The truth about Entra Backup vs. Third-Party ISV tools.Subscribe with your favorite podcast player or watch on YouTube 👇About The GuestsNathan, Ru, and Thomas are highly experienced MVPs specializing in identity security, governance, and Microsoft Entra.Nathan McNulty - LinkedIn - https://www.linkedin.com/in/nathanmcnulty/Ru Campbell - LinkedIn - https://www.linkedin.com/in/rlcam/Thomas Naunheim LinkedIn - https://www.linkedin.com/in/thomasnaunheim/🔗 Related Links* Microsoft Entra Backup and Recovery Documentation - https://learn.microsoft.com/en-us/entra/backup/overview* Microsoft Entra Tenant Governance - https://learn.microsoft.com/en-us/entra/id-governance/tenant-governance/overview* Synced Passkeys - https://learn.microsoft.com/en-us/entra/identity/authentication/how-to-authentication-passkeys-fido2* Microsoft Work IQ CLI (Public Preview) - https://learn.microsoft.com/en-us/microsoft-365/copilot/extensibility/workiq-overview* Playwright https://playwright.dev/* Entra Auth Tracer (Chrome Extension) - https://github.com/darrenjrobinson/EntraAuthTracer* Unified Risk Score - https://learn.microsoft.com/en-us/defender-xdr/investigate-users#risk-score-tab-preview📗 Chapters00:00 Intro to New Entra Features02:04 Entra Backup and Recovery Deep Dive10:41 Difference Reports Explained15:54 Intro to Tenant Governance23:34 Managing Multi-Tenant Organizations33:31 Conditional Access Optimization Agent36:55 The Great Passkey Debate47:22 Retirements: SP-less Auth & ACS for SharePoint48:46 Unified Risk Score in Defender52:38 MVP Tips of the WeekPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Emilien Socchi, Cloud Security Research Engineer at Storebrand, joins us to discuss CA Insight and AZTier.Two open-source tools Emilien built to find gaps in Conditional Access policies and categorize Azure/Entra roles based on attack paths. Learn how CA Insight evaluates 250 million sign-in combinations offline in minutes instead of days, why the What If API doesn't scale, and how AZTier helps defenders and pen testers understand privilege escalation risks across Entra ID, Azure, and Microsoft Graph.Together, these projects help security teams move from reactive log monitoring to a proactive defense strategy.What’s Breaking and Slowing Your Entra ID Environment?In Microsoft Entra ID, the same visibility gaps cause two problems:* Things break* Work slows downExpired client secrets disrupt integrations. Certificates lapse and authentication fails. New apps appear with excessive permissions and no clear ownership. At the same time, teams struggle to answer basic questions, which applications have access to Microsoft 365 data, whether that access is still required, and who is responsible for it.When answers are not immediate, reviews stall and projects slow down.ENow App Governance Accelerator Credential Guard helps identify expiring credentials and expose permission and ownership gaps.For organizations under 10,000 users, pricing ranges from $3,500 to $9,500 annually through March 31, 2026.Subscribe with your favorite podcast player or watch on YouTube 👇About Emilien SocchiEmilien Socchi is a Cloud Security Research Engineer at Storebrand (Oslo, Norway) focusing on the proactive discovery of security issues. With an extensive background in application and cloud penetration testing, Emilien has published practical research and tooling used by defenders. He also maintains several open‑source projects, including Azure administrative tiering models and Entra ID role‑monitoring utilities.LinkedIn - https://www.linkedin.com/in/emilien-socchi🔗 Related Links* CA Insight- https://github.com/emiliensocchi/entra-ca-insight* Azure Administrative Tiering (AzTier) - https://aztier.com* AzTier Source: https://github.com/emiliensocchi/azure-tiering* AzTier Deployer - https://github.com/emiliensocchi/aztier-deployer📗 Chapters00:00 The Story Behind CA Insights16:52 Why the ‘What If’ API Doesn’t Scale 21:09 Building an Offline Evaluation Engine 45:22 Deep Dive into AZTier: A Red Team Perspective Podcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
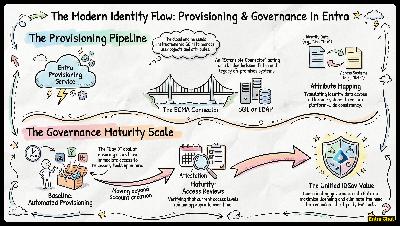
Darren Robinson, Identity and Zero Trust Strategy and Architecture Capability Lead at Increment, shares his extensive experience in identity governance and administration.In this episode Merill sits down with Darren “Doc” Robinson – Microsoft MVP since 2017, former SailPoint Ambassador and one of Australia’s most experienced identity architects.Darren takes us on a 25+ year journey from Novell networks to modern Microsoft Entra ID, reveals why he’s building custom ECMA2 connectors, and shares the exact PowerShell tools he just open-sourced (Granfeldt uplift, ECMA2 Host Tools, Provision On-Demand module).We also compare Entra ID Governance vs SailPoint and dive into his latest obsession: MCPs for Entra News and personal AI agents.Whether you’re migrating legacy apps or levelling up your IGA strategy, this episode is pure gold.Sponsored by CoreView:Would you bet your reputation on your current Microsoft 365 security posture?Sure, you’ve checked Purview. Maybe tightened Conditional Access. We all do that.But it’s usually the quiet stuff that bites... permissions that expanded, policies that drifted, exceptions nobody revisited.You could assume it’s fine.Or you could run the Microsoft 365 Security Posture Check.It’s free.It runs locally.And no, it doesn’t send your tenant data back to us.We’ll even help you set it up.Subscribe with your favorite podcast player or watch on YouTube 👇About Darren RobinsonDarren is highly accomplished in digital identity and cybersecurity specialising in Identity & Access Management for over three decades. Darren is renowned for driving Digital Identity innovation, building global offerings, and leading high-impact teams to deliver cutting-edge solutions that enhance security posture, operational efficiency, and business value.🔗 Related Links* Blog: https://blog.darrenjrobinson.com* GitHub: https://github.com/darrenjrobinson* LinkedIn: https://www.linkedin.com/in/darrenjrobinson/In this episode…1. Understanding the “Metaverse”The foundation of Microsoft’s identity strategy dates back to the acquisition of Zoomit in 2000. This introduced the Metaverse—not a VR world, but a “hologram” or central representation of a user that exists across multiple systems like SQL databases and LDAP directories. By correlating these identities into one object, organizations can maintain consistency across a fragmented environment.2. The Modern Bridge: ECMA and SCIMAs organizations move to the cloud, the “heavy” sync engines like MIM (Microsoft Identity Manager) are being replaced by Entra Cloud Sync. The modern approach uses:* A Light Shim: A small on-premises component that acts as a member of the domain.* SCIM Instructions: The Entra provisioning service sends instructions via the SCIM protocol to this shim.* ECMA Connectors: The Extensible Connector Management Agent (ECMA) translates these cloud instructions into a language legacy on-prem apps can understand, such as SQL or Oracle updates.3. Scaling with PowerShell 7One of the biggest hurdles in legacy identity management was performance. Darren Robinson recently uplifted the popular Granfeldt PowerShell Management Agent to support PowerShell 7. This update allows for:* 64-bit Processing: Handling larger datasets with ease.* Parallelism: Sending multiple identity updates in parallel rather than waiting for individual “gets,” significantly speeding up sync times.4. Managing the “Cache”A common pain point for administrators is the lack of visibility into the ECMA host cache. To solve this, Darren developed a new module that allows practitioners to programmatically query the cache, back up configurations, and document every connector and parameter in the system.Key Takeaway: Whether you are migrating from legacy solutions like Novell or managing a complex hybrid Entra environment, the goal remains the same: automated, secure, and visible identity lifecycles.📗 Chapters00:00 Intro02:22 The Evolution of Directory Services and Synchronization08:05 Understanding Sync Engines and the Metaverse14:45 Modern Identity Provisioning with Entra17:39 Developing Custom PowerShell ECMA Connectors20:53 Automating Provisioning with New PowerShell Modules28:53 The Current Landscape of Identity Governance31:37 Solving the Disconnected Apps Challenge35:46 Exploring Model Context Protocol (MCP)45:34 Leveraging Local AI and LLMs for Identity TasksPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
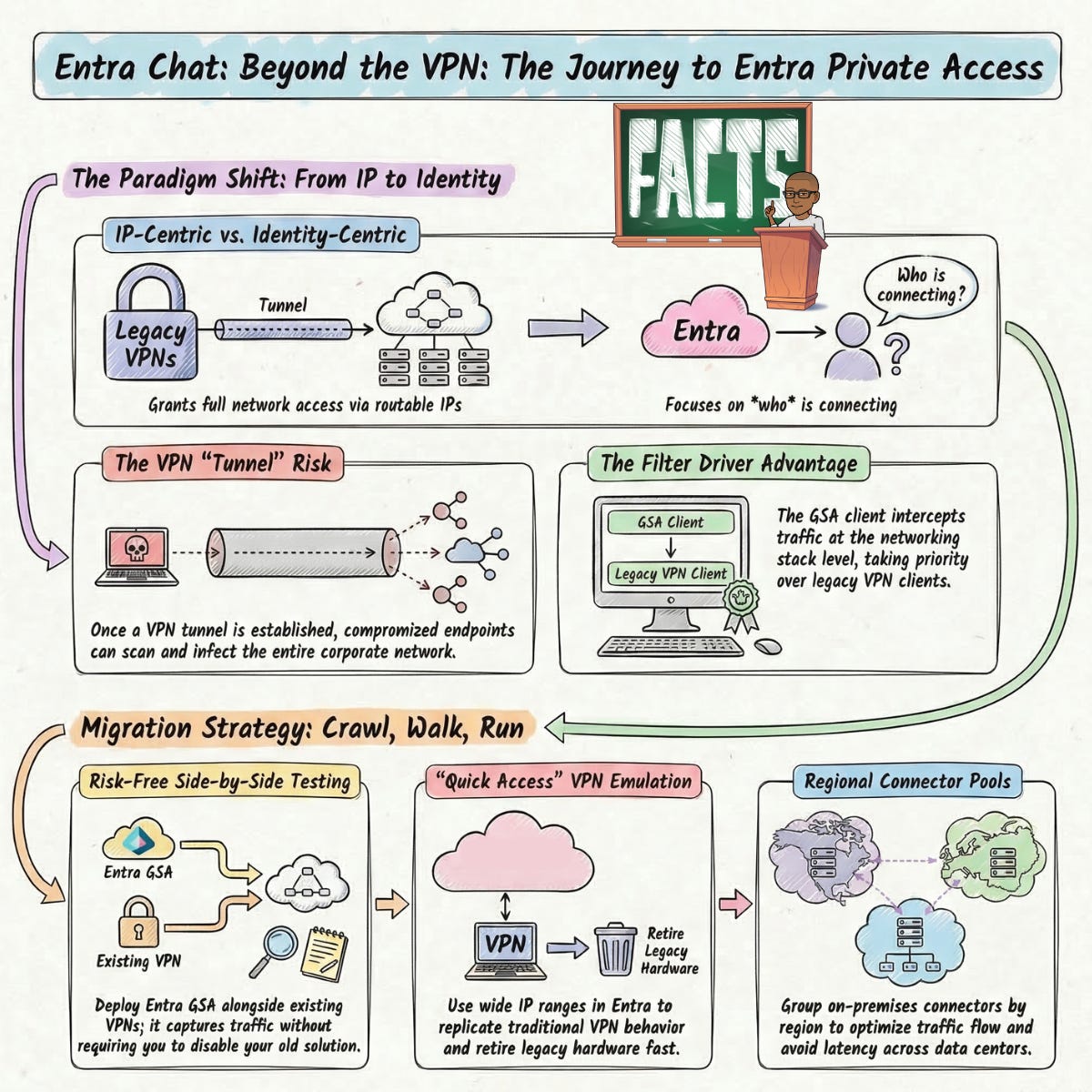
Richard Hicks wrote the book on DirectAccess. Then he wrote the one on Always On VPN. Now he’s here to tell you it’s time to move on from both (and other legacy VPNs). Over the last two years, Richard has helped numerous enterprise customers navigate the shift from legacy VPN to Microsoft Entra Private Access, and he’s collected some hard-learnt lessons along the way that most migration guides won’t tell you.In this episode, Richard - enterprise security consultant and early Entra Private Access insider - breaks down why traditional VPN is fundamentally broken for today’s threat landscape, how Entra Private Access works under the hood, and the exact crawl-walk-run playbook he uses to migrate enterprise customers without disruption. Plus: his hot take on the Microsoft E7 announcement and why it just changed the pricing conversation forever.In this episode you’ll learn:* Why your VPN tunnel is a security liability — and how a single compromised device can expose your entire corporate network* How Entra Private Access works differently to traditional VPN, and why that architectural shift matters for security* The “Quick Access” migration strategy that lets you get off legacy VPN fast, without locking everything down on day one* How to deploy the Global Secure Access client alongside your existing VPN — so you can migrate field-based workers without a single disconnection* What most teams get wrong about the Entra Private Network Connector — and the scaling pitfalls that catch enterprises off guard* Why Conditional Access knowledge, not connectivity, is the real key to a successful zero trust migration* The current limitations of Entra Private Access and how to plan around them* We also discuss the new ‘E7’ which includes Entra Private AccessSubscribe with your favorite podcast player or watch on YouTube 👇About Richard HicksRichard Hicks is the founder and principal consultant at Richard M. Hicks Consulting, Inc. A Microsoft Most Valuable Professional (MVP) with more than 30 years of experience implementing secure remote access and public key infrastructure (PKI) solutions, he is a widely recognized enterprise mobility and security infrastructure expert sought after by organizations worldwide. His mission is to help companies provide visibility, control, and assurance for their field-based users and devices, ensuring the highest level of security and productivity for today’s highly mobile workforce.LinkedIn - https://www.linkedin.com/in/richardhicks/🔗 Related Links* Richard’s Blog - https://directaccess.richardhicks.com/* Richard M. Hicks Consulting, Inc - https://www.richardhicks.com/* https://directaccess.richardhicks.com/always-on-vpn-vs-entra-private-access/📗 Chapters00:00 Intro 01:10 The History of Direct Access and Always On VPN 05:59 Transitioning to Zero Trust and Entra Private Access 11:34 Seamless Side-by-Side VPN Migration 17:37 Using Quick Access to Kickstart Zero Trust 23:43 Changing Mindsets: Identity over IP Addresses 27:55 The New Zero Trust Network Assessment Tool 29:17 Avoiding Pitfalls with the Entra Private Network Connector 33:11 Feature Wishlist: IPv6 and Process Binding 38:46 Hot Takes on the New Entra E7 SuitePodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
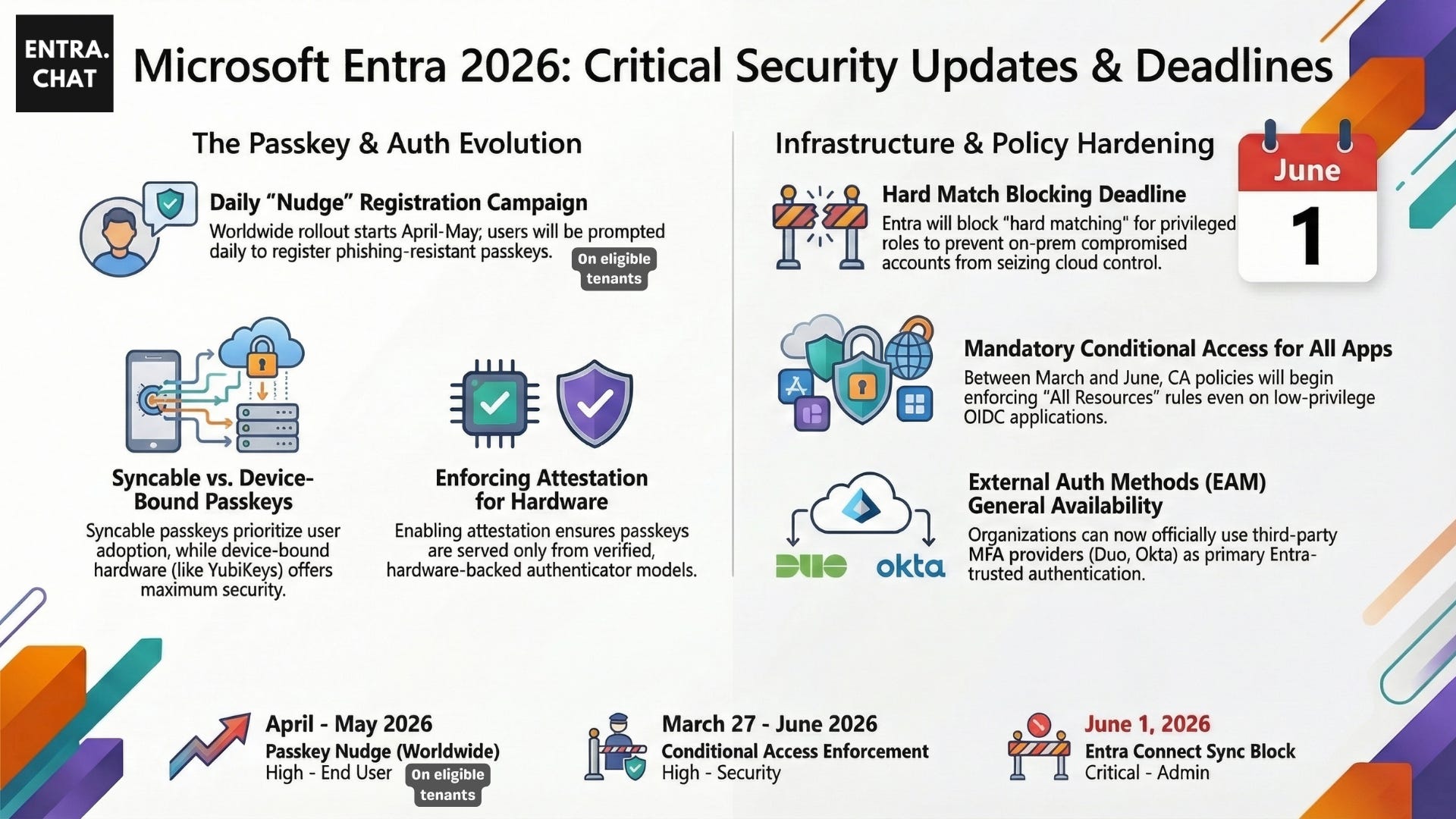
I am back home in Melbourne today, and joining me are Nathan McNulty from Alaska and Daniel Bradley from the UK as we dive into all the massive Entra updates that dropped last month. We are breaking down the controversial shift to syncable passkeys , why your Conditional Access policies might suddenly start blocking apps , and the absolute necessity of moving privileged accounts away from on-prem AD. We’re also geeking out over some incredible new Global Secure Access (GSA) features and how AI is completely transforming the way we work with Graph API. You won’t want to miss the under-the-radar changes that could impact your tenant’s security architecture overnight.Here’s a quick overview of all the topics we covered in this episode (links below).Sponsored by:Scan, Score, and Secure Your Applications in EntraApplication identities represent one of the largest attack surfaces in Entra and are often among the least consistently governed. AppGov Score helps IT and Security teams understand where risk exists. The 24-check assessment evaluates Entra ID application integrations against Microsoft-recommended governance practices, analyzing:* App registrations and enterprise apps for excessive permissions* Expired or unmanaged secrets* Ownerless apps* Risky consent grants, and* Privileged service principalsResults are delivered as a clear, defensible risk score with actionable findings. No scripts. No manual inventory. Just a fast, read-only scan that reveals app sprawl, identity misconfigurations, and blast radius so you can prioritize remediation and strengthen your security posture with confidence.Subscribe with your favorite podcast player or watch on YouTube 👇About Nathan McNultySenior Security Solutions Architect at Patriot Consulting and Microsoft MVP in security. Nathan is the practice lead for identity and has extensive experience with endpoint deployments and everything Entra.LinkedIn - https://www.linkedin.com/in/nathanmcnulty/About Daniel BradleySenior Solution Architect for CDW down in the UK and an MVP in Identity Security and M365 for Graph API. Daniel specializes in pre-sales, mergers, acquisitions, and the highly technical migration space.LinkedIn - https://www.linkedin.com/in/danielbradley2/🔗 Related Links* Entra What's New - https://learn.microsoft.com/en-us/entra/fundamentals/whats-new* Upcoming Conditional Access change: Improved enforcement for policies with resource exclusions - https://techcommunity.microsoft.com/blog/microsoft-entra-blog/upcoming-conditional-access-change-improved-enforcement-for-policies-with-resour/4488925* XDRInternals - https://github.com/MSCloudInternals/XDRInternals* Passkey Login - https://github.com/nathanmcnulty/nathanmcnulty/blob/main/Entra/passkeys/PasskeyLogin.ps1* Graph PM - https://graph.pm📗 Chapters03:01 Syncable Passkeys & Registration Changes18:10 Conditional Access Policy Updates26:35 Blocking Hard Match for Privileged Roles35:42 External Authentication Methods GA43:04 Lifecycle Workflows & Admin Units48:01 Global Secure Access (GSA) BYOD Preview53:06 New My Account Portal & Authenticator Updates58:43 AI Skills & Automating Graph APIPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Hey folks, I have to start with a massive shout-out to Morten Knudsen and his entire team at Experts Live Denmark where I’m just returning from. Organizing an event for over 1,200+ attendees is no small feat, and they pulled it off with incredible energy and precision. It was easily one of the most impressive community gatherings I’ve been a part of.Amidst that massive crowd, I had the privilege of co-leading a deep-dive Identity Masterclass alongside four exceptional Microsoft MVPs: Jan Vidar Elven, Pim Jacobs, Thomas Naunheim, and Klaus Bierschenk.We weren’t sure what to expect, but the response was overwhelming. We had over 120 dedicated attendees who stayed with us for the full 7-hour session - diving deep into the weeds of Entra ID, governance, privileged access, Agent ID and more. Instead of theory-heavy slides, we built a practical, end-to-end governance story.Because we believe this knowledge should be accessible, we are now giving away the labs for free so everyone can skill up, learn, and implement these patterns in their own environments.Here’s the core of what we covered, and what you will learn in this podcast walk through of the labs and what you can try out yourself today!Links to GitHub repo and YouTube video below.Sponsored by:If you’re a systems administrator, you already know – patching is painful. It’s time-consuming, risky, and one small mistake can mean downtime. So, it gets postponed. Again. And again. What if patching was just… Easy?Introducing Action1, a cloud-native patch management platform for Windows, macOS, Linux, and third-party apps. You’ll be up and running in five minutes. No infrastructure to maintain. No complexity.And here’s the best part: you can use Action1 on your first 200 endpoints for free. Forever. No feature limits. No credit card. No hidden tricks. Seriously, It’s NOT a disguised free trial. Too good to be true? Too good and actually true! Check for yourself, go to: on.action1.com/entrachatSo, if you’re looking for an easy-to-use patching tool that would help you save weeks, if not months of your time, go to on.action1.com/entrachat and sign up for “Patching That Just Works”.1️⃣ Inbound Provisioning: Start with a Source of TruthMost identity problems start with one issue:There is no clean, authoritative identity source.We demonstrated how to use Inbound Provisioning in Entra to:* Accept identity payloads via Microsoft Graph* Create users in a disabled state* Capture attributes like hire date, leave date, department* Treat HR (or another system) as the lifecycle authorityWhy this mattersIf identities are manually created:* Joiners are inconsistent* Leavers are missed* Privileged accounts become orphanedInbound provisioning allows you to:* Standardize creation* Attach lifecycle automation immediately* Reduce manual admin overheadKey concept:Provision first. Enable later. Automate everything in between.2️⃣ Lifecycle Workflows: Automate Joiner / Mover / LeaverOnce a user is provisioned, lifecycle workflows take over.We implemented:* Pre-hire workflow* Day-one onboarding workflow* Post-onboarding actionsTriggers included:* Employee hire date* Creation time* Group membership* Attribute changesReal-world onboarding pattern* Account is created disabled* Workflow enables the account at the correct time* Temporary Access Pass (TAP) is generated* TAP is sent securely* Access is assigned automaticallyThis reduces:* Manual enablement* Helpdesk load* Security gapsDesign principle:Automation should enforce timing — not people.3️⃣ Privileged Account Design: Separate the IdentitiesWe had a strong opinion in the session:Admin accounts should be separate and cloud-only.Why?* Syncing privileged accounts from on-prem introduces risk* HR systems should not directly control privileged identities* Governance features work best with cloud-native identitiesWe explored three creation patterns:* Inbound provisioning for privileged accounts* Access Packages (with auto-assignment or request model)* Lifecycle workflows + custom Logic AppsEach has trade-offs.What matters most:Privileged identities must be:* Separately authenticated* Phishing-resistant (FIDO2 or passkeys)* Independently governed* Linked for offboarding4️⃣ Linking Identities for InvestigationOne challenge in Entra:There’s no native “this person owns these 3 accounts” view.We explored identity linking in Microsoft Defender XDR, where:* Multiple accounts can be associated to one identity* Incident investigations become clearer* Privileged activity can be correlated with user contextThis becomes critical during:* Compromise investigations* Insider threat analysis* Lateral movement trackingSecurity takeaway:If you can’t correlate identities, you can’t fully investigate them.5️⃣ Backup & Restore: The Truth About EntraThere is no traditional backup system in Entra.Instead, you have:* Soft-delete (with recycle bin)* Hard-delete (irreversible)* API-based recovery* Configuration export strategiesWe discussed:* Protecting deleted items with Protected Actions* Using Conditional Access to restrict destructive operations* Exporting configuration JSON regularly* Monitoring configuration driftReality:If you aren’t exporting your tenant configuration, recovery becomes manual and painful.Governance is not just about creation — it’s about resilience.6️⃣ Protected Actions + Conditional AccessA powerful but underused feature:Protected Actions.You can require Conditional Access enforcement before allowing:* Hard deletes* Sensitive configuration changesExample:* Only allow permanent deletion from a compliant device* Only allow from a trusted location* Require phishing-resistant authenticationEven Global Admins must pass policy.Security mindset shift:Admin role ≠ unlimited ability.7️⃣ Agent ID & Blueprints: The Future of Identity for AIWe also explored Agent ID — one of the newer capabilities in Entra.Why not just use a service principal?Because agents:* Need stronger guardrails* Must support per-user instances* Require conditional access enforcement* Must be auditable at scaleBlueprints allow:* A parent definition of permissions* Individual agent instances per user* Centralized governance over many agentsAs AI agents scale, identity must scale securely with them.Forward-looking insight:Agent governance will soon be as important as user governance.8️⃣ Design Philosophy Behind the LabThe entire masterclass was built around one principle:Identity is a lifecycle, not a login.We covered:Provision → Enable → Assign → Elevate → Monitor → Protect → Offboard → RecoverIf any step is manual, inconsistent, or undocumented — risk increases.The labs give you a complete pattern you can implement in your own tenant.🎯 What You Should Do Next* Watch/listen to the full podcast where we walk you through the labs.* Go try out the labs at github.com/IdentityMan/MasterclassELDK26 in your own tenant.Subscribe with your favorite podcast player or watch on YouTube 👇About us* Jan Vidar Elven, Security MVP - https://www.linkedin.com/in/janvidarelven* Pim Jacobs, Security MVP - https://www.linkedin.com/in/pimjacobs89* Thomas Naunheim, Security MVP - https://www.linkedin.com/in/thomasnaunheim* Klaus Bierschenk, Security MVP - https://www.linkedin.com/in/klabier🔗 Related Links* https://github.com/IdentityMan/MasterclassELDK26* https://discord.entra.news* https://on.action1.com/entrachat📗 Chapters00:00 Intro 00:50 Open Sourcing the Entra Lab 03:42 Entra ID Inbound Provisioning 08:05 Lifecycle Workflows and Governance 10:57 Securing Privileged Admin Accounts 16:21 Offboarding and Linked Identities 19:51 Sponsor: ActionOne 21:02 Entra ID Backup, Restore & Protected Actions 26:08 Exploring Agent ID and Blueprints 30:28 How to Access the Open Source LabPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
What does it take to migrate 40,000 devices to a cloud-native environment in a massive, complex enterprise? For most IT leaders, the prospect of moving away from 20 years of legacy infrastructure is enough to cause a sleepless night.In our latest episode of Entra Chat, we sat down with enterprise veterans Michael Brunker and Prem Kothandapani to deconstruct their recent, massive rollout. They successfully converted nearly 40,000 devices from on-premises Active Directory to Entra Joined in just nine to ten months—all with a lean team of 10–15 people.Here are the high-stakes lessons they learned from the trenches of modern management.The “Nuclear Option”: Cleaning Up 20 Years of GPO DebtOne of the most controversial decisions the team made was what they called the “nuclear option” regarding Group Policy Objects (GPOs). Instead of porting over decades of legacy policies that no one fully understood, they chose to start from scratch.By building a new security baseline from the ground up in Intune, they ensured the new environment was clean, modern, and free from the “stale” configurations that often plague legacy estates.Killing the “VPN Tax”For the end user, the primary driver for this migration was a radically improved experience. In a cloud-native world, the dependency on legacy VPN technology disappears.* Work from Anywhere: Users can sign on and get access without the friction of starting a VPN or worrying about office cabling.* Security at the Edge: Moving to Entra ID shrinks the attack surface by removing devices as a direct entry point to your core on-prem Active Directory.Sponsored by:If you’re a systems administrator, you already know – patching is painful. It’s time-consuming, risky, and one small mistake can mean downtime. So, it gets postponed. Again. And again. What if patching was just… Easy?Introducing Action1, a cloud-native patch management platform for Windows, macOS, Linux, and third-party apps. You’ll be up and running in five minutes. No infrastructure to maintain. No complexity.And here’s the best part: you can use Action1 on your first 200 endpoints for free. Forever. No feature limits. No credit card. No hidden tricks. Seriously, It’s NOT a disguised free trial. Too good to be true? Too good and actually true! Check for yourself, go to: on.action1.com/entrachatSo, if you’re looking for an easy-to-use patching tool that would help you save weeks, if not months of your time, go to on.action1.com/entrachat and sign up for “Patching That Just Works”.The “Gnarly” Problems: What Breaks First?Success wasn’t just about the big picture; it was about mastering the “fundamental basic building blocks”. Michael and Prem highlighted several technical hurdles that can derail a migration if not handled early:* The Proxy Trap: Many organizations fail to update their proxy server allow-lists with the specific Microsoft URLs required for cloud authentication.* App Authentication: Moving from Kerberos-based device auth to OAuth and modern cloud flows requires rigorous testing across different “personas,” such as front line workers versus corporate office users.The Secret to Scaling: Small Teams, Big StrategyPerhaps the most surprising takeaway was that a project of this scale didn’t require an army. By focusing on a “small team” of highly skilled engineers and dedicated communications experts, they maintained momentum and avoided “stop-start” migration fatigue.Want to hear the full technical breakdown, including how they handled zero-downtime requirements for front line workers?Subscribe with your favorite podcast player or watch on YouTube 👇About Michael BrunkerMichael Brunker has approaching 40 years in the IT industry and has operated as an enterprise architect across major organizations like BP, Woodside, and Telstra. LinkedIn - https://www.linkedin.com/in/michaelbrunker/About Prem KothandapaniPrem Kothandapani is an EndPoint Architect with over 14 years of experience in endpoint computing and major migrations, having worked at NBN, Australian Unity, and Telstra.LinkedIn - https://www.linkedin.com/in/premnath-kothandapani-41744153/📗 Chapters00:00 Cloud-Native Device Management 02:58 The True Cost of Legacy Infrastructure 07:47 Moving to Modern Management 11:13 The Blueprint for a 40,000 Device Migration 20:07 Handling Complex App Dependencies 28:07 Crafting a Seamless User Migration Experience 33:28 Automating with Graph API and Autopilot 43:09 Avoiding the Co-Management Trap 55:01 The New Starter Experience 57:24 Migration Velocity and Lessons LearnedPodcast Apps🎙️ Entra.Chat - https://entra.chat 🎧 Apple Podcast → https://entra.chat/apple 📺 YouTube → https://entra.chat/youtube 📺 Spotify → https://entra.chat/spotify 🎧 Overcast → https://entra.chat/overcast 🎧 Pocketcast → https://entra.chat/pocketcast 🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx 👔 LinkedIn → linkedin.com/in/merill 🐤 Twitter → twitter.com/merill 🕺 TikTok → tiktok.com/@merillf 🦋 Bluesky → bsky.app/profile/merill.net 🐘 Mastodon → infosec.exchange/@merill 🧵 Threads → threads.net/@merillf 🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
March 2026 is shaping up to be one of the most important months for Microsoft Entra ID administrators in recent memory.Microsoft is automatically enabling passkey profiles in Entra ID, and if you don’t configure them yourself, your tenant will be migrated with default settings.In this episode of Entra Chat, I sat down with Microsoft Security MVPs Daniel Bradley and Ewelina Paskowska to break down what this really means for Microsoft 365 administrators.But passkeys aren’t the only story this month.1️⃣ Passkey Profiles Are Becoming the DefaultStarting March 2026:* Passkey profiles will be auto-enabled* Tenants that haven’t configured profiles will be migrated* Registration campaigns will shift from Authenticator-first to passkey-firstThis is a major shift toward phishing-resistant authentication.You’ll now be able to:* Separate hardware-backed vs synced passkeys* Apply granular group-based controls* Enforce stronger authentication for privileged users2️⃣ Source of Authority Conversion Is Finally GAFor years, admins used messy delete-and-restore hacks to convert synced users to cloud-only.Now it’s officially supported.You can convert individual users from on-premises authority to cloud-managed — without breaking hybrid entirely.Why this matters:* Easier M&A transitions* Full access to Entra ID Governance features* Cleaner lifecycle management* Reduced dependency on legacy infrastructureFor hybrid environments moving toward cloud-first identity, this is huge.Sponsored by:If you are a systems administrator managing endpoints every day, you’ve probably postponed patching at least once — not because you forgot… But because you didn’t feel like gambling with uptime. Meanwhile, the backlog grows, vulnerabilities pile up, and patching stays stuck in manual mode.Action1 fixes that.Action1 is a cloud-native patch management platform for Windows, macOS, Linux, and third-party apps — all from one place, no VPN needed. Curious how easy it is to start? You can use it on your first 200 endpoints, for free, forever, with no functional limits. It’s not a disguised free trial. No credit card required, no hidden limits, no tricks.All you have to do is visit on.action1.com/entrachat and get started today.So, if you’re looking to automate patching at scale and get weeks— even months—of your time back, go to on.action1.com/entrachat and sign up for patching—that—just—works.3️⃣ App Registration Deactivation (A Quietly Powerful Feature)Microsoft added the ability to deactivate app registrations.Instead of deleting an app (and losing configuration), you can now:* Immediately stop token issuance* Preserve metadata and permissions* Investigate safely* Re-enable without rebuildingFor incident response scenarios — especially in multi-tenant or MSP environments — this is a big step forward.4️⃣ Conditional Access Behavior ChangesThere’s also a change impacting tenants with Conditional Access policies targeting “All resources” but excluding certain apps.Previously, certain minimal-scope apps could bypass enforcement under specific conditions.That loophole is closing.Admins should:* Review message center notifications* Audit legacy apps* Validate MFA handling before rolloutAs always with identity changes: being proactive is critical.5️⃣ Sync Security Hardening (Hard Match Protection)Microsoft is adding additional validation to protect against malicious hard matching scenarios in hybrid environments.This reduces the risk of identity takeover via manipulated on-prem objects.It’s automatic — but important to understand if you manage hybrid identity or MSP transitions.Watch the full episode for the deep technical breakdown and real-world implications.Subscribe with your favorite podcast player or watch on YouTube 👇About Daniel BradleyDaniel is a Senior Solution Architect for CDW and Microsoft MVP in Identity & Graph API. He is a avid writer who enjoys investigating new features and building practical tools to share with the community through his blog. He also is one of the moderators for the r/entra subreddit.* Website: https://ourcloudnetwork.com* LinkedIn: https://www.linkedin.com/in/danielbradley2* X: https://x.com/DanielatOCNAbout Ewelina PaczkowskaEwelina is a Solution Architect at Theatscape and a Microsoft Security MVP. She is a content creator and speaker who enjoys breaking down complex solutions into clear, practical guidance. Ewelina is also an organiser of the Microsoft 365 Security & Compliance user group and the creator behind Welka’s World, where she shares insights and real-world knowledge around Microsoft security and compliance.* Website: https://welkasworld.com* LinkedIn: https://www.linkedin.com/in/ewelinapaczkowska* X: https://x.com/WelkasWorld🔗 Related Links* MC1221452 - Microsoft Entra ID: Auto-enabling passkey profiles - https://mc.merill.net/message/MC1221452* Ability to convert Source of Authority of synced on-prem AD users to cloud users is now available - https://learn.microsoft.com/en-us/entra/identity/hybrid/user-source-of-authority-overview* Service Principal creation audit logs for alerting & monitoring - https://learn.microsoft.com/en-us/entra/identity/monitoring-health/understand-service-principal-creation-with-new-audit-log-properties* Deactivate an app registration - https://learn.microsoft.com/en-us/entra/identity/enterprise-apps/deactivate-app-registration* MC1223829 - Upcoming Conditional Access change: Improved enforcement for policies with resource exclusions - https://mc.merill.net/message/MC1223829* Microsoft Entra Connect security hardening to prevent user account takeover - https://learn.microsoft.com/en-us/entra/fundamentals/whats-new#general-availability---microsoft-entra-connect-security-hardening-to-prevent-user-account-takeover📗 Chapters06:16 Converting Source of Authority to Cloud 15:37 Auto-Enabling Passkey Profiles 24:33 Deactivating App Registrations 31:56 Conditional Access for Excluded Apps 38:48 Sync Jacking Protection 41:45 Unified Tenant Configuration Management 46:31 Service Principal Creation LogsPodcast Apps🎙️ Entra.Chat → https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Governance in Microsoft 365 has always been hard. Not because the tools didn’t exist, but because scale, complexity, and change made consistency almost impossible. As tenants grow, so do the challenges of configuration drift, manual admin changes, and inconsistent environments.For years, admins have relied on scripts, tribal knowledge, and community-led solutions like Microsoft 365 Desired State Configuration (M365DSC) to manage this “policy sprawl”. While M365DSC was a groundbreaking open-source effort, it often faced a steep learning curve and lacked official Microsoft support.Until now.In this episode of Entra Chat, we sit down with Nik Charlebois, Principal Program Manager at Microsoft and the original visionary behind M365DSC. Nik now leads the charge for one of the most significant platform shifts in Microsoft 365 administration: Tenant Configuration Management (TCM).Shadow IT and SaaS sprawl are outpacing IT teamsIt can feel impossible to tackle these app governance challenges:📦 Entra ID isn’t secure by default💥 SaaS adoption & sprawl isn’t slowing down⌨️ Citizen Development keeps rising (hello, Copilot Studio!)🗑️ Vendors often don’t remove apps after uninstall🔃 Offboarding is inconsistent or doesn’t happen at all🥔 App governance is passed around like a hot potatoENow AppGov Score shines a light on lurking risks, providing a free App Governance Benchmark Report for your Entra tenant. Reclaim control and protect against breach & disruptions. Free upgrade to Standard Tier for 7 days once you get your score.What is Tenant Configuration Management?TCM is Microsoft’s official “Config as Code” platform for M365. Built directly on top of the Microsoft Graph, it represents a new operating model for how tenants are governed.Key features discussed in this episode include:* Official Support: Moving beyond best-effort community maintenance to a fully supported Microsoft solution.* Simplified Experience: Transitioning from cryptic MOF files to human-readable JSON templates, significantly lowering the learning curve for admins.* Snapshot & Drift Detection: The ability to capture “snapshots” of your tenant’s current state and monitor for unauthorized changes.* Automatic Remediation: Automatically reverting detected configuration drifts back to your defined “gold standard” state.* Broad Coverage: Support for core workloads including Entra ID, Exchange, Intune, Purview, Defender, and Teams with more to come.This isn’t just a new feature; it’s the evolution of tenant governance into a native, API-driven platform. Tune in to hear Nik explain how TCM is bridging the gap between community innovation and official enterprise-grade management.Listen to the full episode now to learn how to start your journey with the TCM public preview!Subscribe with your favorite podcast player or watch on YouTube 👇About Nik CharleboisNik is a Principal Program Manager at Microsoft leading the Microsoft 365 configuration-as-code efforts. Ex-MVP, speaker, blogger, and author, he leads the configuration-as-code efforts for Microsoft 365.LinkedIn - https://linkedin.com/in/nikcharlebois🔗 Related Links* Nik’s Blog - https://nikcharlebois.com/* Overview of the unified tenant configuration management APIs - https://learn.microsoft.com/en-us/graph/unified-tenant-configuration-management-concept-overview📗 Chapters00:00 Intro 03:44 Origin of M365DSC 07:51 Introducing Tenant Config Management 09:24 Supported Workloads 11:15 Control Plane vs Data Plane 14:26 DSC vs TCM Architecture 15:22 Snapshots and Monitors 18:56 Managing Drift Across Environments 28:03 Licensing and Limits 32:48 Authentication and Permissions 37:53 Getting StartedPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
In this episode, we sit down with Eric Woodruff, Chief Identity Architect at Semperis, to discuss the reality of achieving a 100% phishing-resistant environment. Over the course of just three months, Eric led a 600-person organization through a complete rollout of passkeys, Windows Hello for Business, and Platform SSO. This conversation moves beyond the technical “knobs and dials” to explore why organizational change management and C-suite buy-in are the true foundations of a successful identity modernization project.Eric shares the creative strategies his team used to drive adoption, including a custom self-enrollment portal built with Power Platform that allowed early adopters to “dogfood” the technology. We dive into the “voluntold” phase of the rollout, where voluntary participation transitioned into mandatory policy, and how they used Power BI to track progress and identify “stragglers”. The episode also provides a transparent look at the technical hurdles encountered, from legacy application exclusions to troubleshooting older Android devices and niche browsers.Looking ahead, we discuss the critical importance of protecting against “downgrade attacks,” where sophisticated phishing attempts try to bypass modern security by tricking users into traditional password entries. Eric emphasizes that the final mile of this journey—removing passwords entirely—is as much about supporting your helpdesk and documenting processes as it is about the technology itself. Whether you are managing a cloud-only tenant or navigating complex hybrid scenarios, this episode offers a practical roadmap for the future of enterprise identity.Subscribe with your favorite podcast player or watch on YouTube 👇About Eric WoodruffThroughout his 25-year career in the IT field, Eric has sought out and held a diverse range of roles. Currently the Chief Identity Architect for Semperis; Eric previously was a member of the Security Research and Product teams. Prior to Semperis, Eric worked as a Security and Identity Architect at Microsoft partners, spent time working at Microsoft as a Sr. Premier Field Engineer, and spent almost 15 years in the public sector, with 10 of them as a technical manager.LinkedIn - https://www.linkedin.com/in/ericonidentity/🔗 Related Links* Phishing-resistant passwordless authentication deployment in Microsoft Entra ID* Semperis Research Uncovers Ongoing Risk from nOAuth Vulnerability in Microsoft Entra ID, Affecting Enterprise SaaS Applications* ConsentFix: Analysing a browser-native ClickFix-style attack that hijacks OAuth consent grants* Meet Silver SAML: Golden SAML in the Cloud* Manage tokens for Zero Trust📗 Chapters02:50 Rolling Out Passkeys 06:47 Application and Device Issues 09:49 Identifying Password Users 12:15 Lessons Learned for 2026 15:14 Understanding Downgrade Attacks 20:10 The NoAuth Vulnerability 27:08 Silver SAML Explained 32:56 Managing Service Principals 38:15 The Consent Fix AttackPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Service principals worked for static apps, but AI agents are different—they make autonomous decisions using LLMs and require a new approach to identity and security.In this episode of Entra Chat, Padma Parthasarathy, Product Manager for Microsoft Entra Agent Registry, explains why Microsoft created Entra Agent Registry and Agent ID, and how they provide identity, governance, and security for AI agents.We cover agent collections, discovery policies, integration with identity protection, and how custom security attributes automate AI agent governance at scale. You’ll also see how agents discover other agents by skills, how global and quarantine collections control visibility, and why these capabilities are critical for enterprise AI security.This is a must-watch (listen) for identity, security, and platform architects preparing for AI at scale.Subscribe with your favorite podcast player or watch on YouTube 👇About PadmaWith close to 20 years of experience in Identity, Security, and enterprise platforms, Padma Prasad Parthasarathy currently leads product and architecture for Security for AI and Agent Identity at Microsoft. He has built and scaled IAM and Zero Trust solutions across some of the world’s largest organizations, bridging deep technical expertise with real-world product impact.LinkedIn - https://www.linkedin.com/in/padmaprasadp/🔗 Related Links* What is the Microsoft Entra Agent Registry? - https://learn.microsoft.com/en-us/entra/agent-id/identity-platform/what-is-agent-registry📗 Chapters00:00 Intro 02:14 The Rise of Digital Workers 07:13 Static Apps vs. AI Agents 12:43 Introducing Entra Agent Registry 17:28 Agent ID vs. Registry 24:08 How Agents Collaborate 30:29 Emerging Agent Standards 35:24 Understanding Agent Collections 42:05 Managing Risky Agents 46:01 Automating Agent SecurityPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
In this episode, I’m joined by Christopher Brumm from glueckkanja to discuss real-world experiences deploying Microsoft Entra Global Secure Access (GSA).We go beyond the docs to talk about actual customer rollouts, scaling challenges, retiring VPNs, and what teams often underestimate when moving to Zero Trust Network Access.Subscribe with your favorite podcast player or watch on YouTube 👇About Christopher BrummChristopher Brumm is a Cyber Security Architect at glueckkanja AG in Germany. With more than 15 years of experience in IT security, Chris brings deep expertise and hands-on knowledge across the Microsoft Security portfolio and beyond. His career journey spans from network and data center technologies to Active Directory and Entra ID, with a strong focus on identity security.As a Microsoft MVP and CISSP, Chris is an active voice in the security community, regularly speaking at events and sharing insights through blog posts on identity and security topics. His latest passion is Global Secure Access, where identity, security, and networking converge to deliver a holistic Zero Trust approach.* LinkedIn - https://www.linkedin.com/in/christopherbrumm🔗 Related Links* Blog - https://chris-brumm.com📗 Chapters04:46 Proof of Concept vs Pilot 12:19 Deployment Strategy: The Blue Pill Approach 16:03 Solving Performance with Intelligent Local Access 17:49 Navigating Networking Challenges 25:14 The Hardest Part: Shutting Down Legacy VPNs 27:38 Handling External Access and BYOD 32:15 B2B Features and Tenant Switching 46:05 Why You Need the Microsoft 365 Profile 50:49 The Ultimate Admin Workstation SecurityPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Nicolas Blank, Founder of NBConsult and a 20-year Microsoft MVP, joins the show to dismantle the complexity around Zero Trust.Most Zero Trust conversations fail because they start with technology. Nicolas flips the script by using powerful everyday analogies (locking your car, protecting your newborn) to land the three core principles with executives.Essential watching for anyone implementing Zero Trust, securing Microsoft 365/Entra ID, or needing leadership support in 2026.Subscribe with your favorite podcast player or watch on YouTube 👇About Nicholas BlankNicolas is the founder, as well an architect, author and speaker focused on Office 365 and Azure at NBConsult in South Africa, England and Hong Kong. Nicolas is a Microsoft Certified Master, Dual Microsoft MVP - Microsoft Office Apps and Services, Microsoft Azure since March 2007.Nicolas has co-authored the Microsoft Zero Trust Adoption Framework https://aka.ms/zero-trust-adopt, published by Microsoft; “Microsoft Exchange Server 2013: Design, Deploy and Deliver an Enterprise Messaging Solution”, published by Sybex and available on Amazon; as well as authoring “Azure Site Recovery: IaaS Migration and Disaster Recovery”, published by Pluralsight.Nicolas can be found on LinkedIn: https://www.linkedin.com/in/nicolasblank/Or via his Company Website: https://www.nbconsult.co🔗 Related Links* Microsoft Zero Trust Workshop - https://aka.ms/ztworkshop* Zero Trust Adoption Framework - https://aka.ms/zero-trust-adopt* Microsoft Digital Defense Report - http://aka.ms/mddr📗 Chapters01:52 The Why Behind Zero Trust 04:17 The Baby Analogy: Explaining Least Privilege 07:41 Debunking Security Myths 11:43 Assume Breach vs Being Secure 15:28 Getting Stakeholder Buy-in 20:24 The Immune System Approach 21:45 Ruining Attacker ROI 25:50 The 96% Statistic You Can’t Ignore 33:24 Where to Start: Practical Tools 37:54 The Zero Trust Adoption FrameworkPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Is the traditional VPN dead? In the latest episode of Entra Chat, we dive deep Microsoft Entra Global Secure Access (GSA).Joined by Karen Simmel from the GSA product team and Thomas from the Entra CXE Architecture team, we explore how Microsoft is bridging the gap between identity and network security.The Shift from VPN to SASEThe "good old days" of spinning up firewalls and DMZs are fading. Traditional controls are often too coarse-grained and lack identity awareness. As Thomas explains, the COVID-19 pandemic accelerated the need for change when traditional VPN gateways physically couldn't handle the load of remote workforces.This has paved the way for SASE (Secure Access Service Edge) and SSE (Security Service Edge), which move security controls to the cloud at hyperscale.What is Global Secure Access?The team breaks down the confusing terminology to help you understand the core products:* Microsoft Entra Private Access: This is the ZTNA (Zero Trust Network Access) solution, replacing the classic VPN for accessing on-prem and private resources.* Microsoft Entra Internet Access: This acts as a Secure Web Gateway (SWG), protecting outbound access to SaaS apps and the internet with URL filtering and DLP controls.* Microsoft Entra Suite: A bundle that combines these network capabilities with Verified ID, Identity Governance, and Identity Protection for a comprehensive solution.The "Secret Sauce"Why choose Microsoft's solution? The differentiator is that GSA isn't just integrated with the Identity Provider (IdP)—it *is* part of the IdP.This deep integration allows for near real-time security. For example, if a user's device is compromised, the SOC team can revoke the token, and Entra can immediately terminate the network tunnel or prompt for step-up authentication. It brings the power of Conditional Access directly to network traffic.Better Performance, Better PrivacyContrary to the belief that security slows things down, GSA often improves performance. By leveraging Microsoft's massive global private fiber network, traffic is intelligently routed to the closest point of presence rather than being backhauled to a headquarters.From a privacy standpoint, admins have granular control. You decide what traffic is tunneled and inspected, ensuring you can meet compliance requirements (like those in the EU) without over-monitoring employee activity.Ready to Deploy?Deployment doesn't have to take months. Some customers are getting up and running with a Proof of Concept (PoC) in a single day. Whether you use the client-based agent or need client-less access for contractors, Microsoft provides detailed deployment plans to guide you.Subscribe with your favorite podcast player or watch on YouTube 👇About the GuestsKeren SemelKeren leads visibility and data insights for the Global Secure Access product group. Based in Tel Aviv, she brings deep experience from the SASE/SSE market to Microsoft.LinkedIn: https://www.linkedin.com/in/keren-semel-4876383/Thomas Detzner Thomas is a lead architect in the Entra CxE team, specializing in Global Secure Access and Zero Trust. A former network engineer based near Munich, he helps organizations bridge the gap between traditional networking and modern identity security.LinkedIn: https://www.linkedin.com/in/thomasdetzner/🔗 Related Links* Microsoft Global Secure Access Documentation - https://learn.microsoft.com/en-us/entra/global-secure-access/ * Zero Trust Workshop - https://aka.ms/ztworkshop📗 Chapters00:00 Intro 05:17 The Limitations of Legacy VPNs 12:49 SASE vs SSE vs ZTNA Explained 21:26 The Identity-Network Secret Sauce 29:42 Unpacking Entra Suite 33:20 Microsoft’s Global Network Architecture 38:19 Client and Clientless Connectivity 41:26 Deployment and POC Process 45:31 Migrating from Zscaler to GSA 47:15 Privacy and Compliance ControlsPodcast Apps🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Louis Mastelinck, a Microsoft MVP and Security Consultant at Proximus NXT, joins me to discuss the critical journey of moving organizations away from SMS-based MFA.We deep dive into a practical strategy for migrating users to the Authenticator app, starting with “stopping the bleed” and managing user groups. We also explore a significant security blind spot regarding Email OTP for SharePoint guest access and how to resolve it. Finally, we debate the future of authentication with device-bound versus synced Passkeys and how to defend against downgrade attacks.Subscribe with your favorite podcast player or watch on YouTube 👇About Louis MastelinckLouis Mastelinck is a Security Consultant at Proximus NXT and a recognized Microsoft MVP based in Belgium. Specializing in Incident Response and the full Microsoft Security stack (including MDE, MDO, Sentinel, and Identity Management), he is dedicated to neutralizing threats and securing digital environments. A GCFA-certified professional, Louis is known for his deep technical expertise in areas like Conditional Access and authentication methods.LinkedIn - https://www.linkedin.com/in/louismastelinck/ 🔗 Related Links* Microsoft: Hang up on SMS - http://aka.ms/hangup📗 Chapters00:00 Intro 00:52 Props and PIM 01:41 The Dangers of SMS MFA 04:51 Strategy: Stopping the Bleed 10:06 Migrating Existing Users off SMS 19:20 Impact on Self-Service Password Reset 22:39 The SharePoint Email OTP Security Gap 25:13 Enabling Entra B2B Integration 34:28 Passkeys: Device-Bound vs Synced 44:40 Defending Against MFA Downgrade AttacksPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
In this week’s episode Jan Bakker, Microsoft MVP and solution architect from the Netherlands, joins us for a masterclass in extending Microsoft Entra ID beyond out-of-the-box capabilities. This episode is your complete guide to building custom identity governance and lifecycle management using Power Apps, Logic Apps, and Azure automation.You’ll learn the fundamental building blocks of automation in the Microsoft ecosystem and how to combine them creatively.Jan’s approach: treat Entra as a platform, not just a product.The automation stack he teaches: → Power Automate (everyday workflows)→ Logic Apps (enterprise automation)→ Dynamic Groups (intelligent triggers)→ Graph API (the foundation of everything)→ Event Hub (cost-effective event streaming)Key topics covered:* Understanding Power Automate vs Azure Logic Apps (and when to use each)* Managed identities and least privilege automation* Dynamic groups as automation triggers* Event Hub for cost-effective event-driven workflows* Custom authentication extensions and token augmentation* Real implementation costs ($50/month for enterprise solutions!)From the conversation:* Step-by-step temporary access pass automation* Automatic refresh token revocation on account disable* MFA method change notifications (like Gmail/Twitter)* Guest lifecycle management and approval flows* Conditional access policy monitoringWhether you’re new to automation or an experienced architect, you’ll walk away with actionable ideas and a new way of thinking about identity solutions.Subscribe with your favorite podcast player or watch on YouTube 👇About Jan BakkerJan is a Microsoft MVP and Solution Architect based in the Netherlands. He is known for his ability to make complex DevOps and Entra concepts accessible and publishes extensive guides on his blog about extending Entra capabilities.LinkedIn: https://www.linkedin.com/in/jan-bakker/🔗 Related Links* Send an email on a new MFA method registration - https://janbakker.tech/send-an-email-on-a-new-azure-mfa-method-registration/* How to build a PowerApp – Temporary Access Pass Manager - https://janbakker.tech/category/power-platform/* Trigger Logic App on group membership changes in Entra ID - https://janbakker.tech/trigger-logic-app-on-group-membership-changes-in-entra-id/* Poor man’s IGA: Monitor and clean up stale guest accounts - https://janbakker.tech/poor-mans-iga-monitor-and-clean-up-stale-guest-accounts/* Poor man’s IGA: Generate Temporary Access Pass for joiners - https://janbakker.tech/poor-mans-iga-generate-temporary-access-pass-for-joiners/* Unlocking the Power of employeeHireDate in Entra ID Dynamic Groups - https://janbakker.tech/unlocking-the-power-of-employeehiredate-in-entra-id-dynamic-groups/* Temporary exclusions for Conditional Access using PIM for Groups - https://janbakker.tech/temporary-exclusions-for-conditional-access-using-pim-for-groups/Sponsored by:Shadow IT and SaaS sprawl are outpacing IT teamsIt can feel impossible to tackle these app governance challenges:📦 Entra ID isn’t secure by default💥 SaaS adoption & sprawl isn’t slowing down⌨️ Citizen Development keeps rising (hello, Copilot Studio!)🗑️ Vendors often don’t remove apps after uninstall🔃 Offboarding is inconsistent or doesn’t happen at all🥔 App governance is passed around like a hot potatoENow AppGov Score shines a light on lurking risks, providing a free App Governance Benchmark Report for your Entra tenant. Reclaim control and protect against breach & disruptions. Free upgrade to Standard Tier for 7 days once you get your score.Secure & Govern Entra Apps Now📗 Chapters00:03 The Poor Man’s IGA Concept 00:07 Revoking Refresh Tokens Automatically 00:13 Power Apps for Approval Workflows 00:16 Custom Logic for Managing Guest Access 00:19 Building a Temporary Access Pass Tool 00:25 Power Automate vs. Azure Logic Apps 00:28 Triggering Automation with Event Hubs 00:31 Alerting on Security Changes via Audit Logs 00:41 Self-Service Group Management 00:44 Why You Must Learn Graph APIPodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Khurram, a key member of the internal App Governance assessment team at Microsoft, joins the show to pull back the curtain on how Microsoft manages application security at a massive corporate scale and the rigorous internal security measures Microsoft employs to protect its corporate Entra ID tenant from risky applications.In this deep dive, Khurram reveals Microsoft’s custom-built App Governance blueprint. He details the process for reviewing and consenting to the hundreds of new application requests the organization receives monthly.Key Takeaways* Permission Risk Rating: Learn how Microsoft’s team assesses and assigns a severity rating—Low, Moderate, Important, or Critical—to permissions. This rating is based on the permission’s capability, whether it’s delegated or application, and its potential for PII exposure (e.g., Application permission or a .all scope will score higher).* The Weighting Model: Discover how the Microsoft app assessment team has proactively risk-rated between 3,000 and 3,500 permissions. This approach dictates when an app is automatically approved (for low-risk requests like User.Read) versus when it is flagged for manual, scenario-based review.* Holistic Risk Review: Khurram explains how the app’s overall risk is calculated beyond just permissions. This includes mandatory security controls like banning high-risk reply URLs (e.g., azurewebsites.net and aka.ms) , enforcing the use of certificates over secrets , and requiring multiple owners.* Multi-Team Veto Power: Understand the critical approval workflow where requests for higher-risk permissions are routed to specific organizational data owners (like the DLP, Identity, or Exchange teams). All teams must approve the request as a whole, giving each team a critical veto power over access to their services.Subscribe with your favorite podcast player or watch on YouTube 👇About Khurram ChaudharyKhurram is a Principal Security Assurance Eng on the internal assessment team at Microsoft. He specializes in App Governance and was instrumental in developing the systems and risk-rating methodologies used to manage thousands of application requests within Microsoft’s corporate tenant.🔗 Related Links* Entra Application Management - https://learn.microsoft.com/en-us/entra/identity/enterprise-appsSponsored by:Shadow IT and SaaS sprawl are outpacing IT teamsIt can feel impossible to tackle these app governance challenges:📦 Entra ID isn’t secure by default💥 SaaS adoption & sprawl isn’t slowing down⌨️ Citizen Development keeps rising (hello, Copilot Studio!)🗑️ Vendors often don’t remove apps after uninstall🔃 Offboarding is inconsistent or doesn’t happen at all🥔 App governance is passed around like a hot potatoENow AppGov Score shines a light on lurking risks, providing a free App Governance Benchmark Report for your Entra tenant. Reclaim control and protect against breach & disruptions. Free upgrade to Standard Tier for 7 days once you get your score.Secure & Govern Entra Apps Now📗 Chapters01:21 The Shift to Admin Consent 03:38 Factors for Reviewing App Risk 06:35 How We Rate Permission Severity 09:25 Automating Low-Risk Approvals 14:17 The Internal Review Workflow 21:40 The App Governance Scoring System 29:01 The Localhost Redirect Debate 39:35 Handling Stale Apps and Permissions 49:34 Advice for Identity AdminsPodcast Apps🎙️ Entra.Chat → https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
Luca Spolidoro from the Microsoft Entra AI Innovations team joins us to unveil the new Microsoft MCP Server for Enterprise. We discuss how this innovation allows admins and AI agents to interface with their tenant using natural language, bridging the gap between LLMs and the complexity of Microsoft Graph.We also talk about the technical challenges of token limits, the patented “three-tool” solution that optimizes queries, and the roadmap for write operations and PowerShell script generation.Subscribe with your favorite podcast player or watch on YouTube 👇About Luca Spolidoro Luca is a Product Manager on the Entra AI Innovations team at Microsoft. Formerly working on advanced queries for Microsoft Graph, he now focuses on enabling AI agents to interact securely and efficiently with directory objects and tenant data. LinkedIn - https://www.linkedin.com/in/lucaspolidoro/🔗 Related Links * Microsoft MCP Server for Enterprise - https://aka.ms/mcp/entraSponsored by:Shadow IT and SaaS sprawl are outpacing IT teamsIt can feel impossible to tackle these app governance challenges:📦 Entra ID isn’t secure by default💥 SaaS adoption & sprawl isn’t slowing down⌨️ Citizen Development keeps rising (hello, Copilot Studio!)🗑️ Vendors often don’t remove apps after uninstall🔃 Offboarding is inconsistent or doesn’t happen at all🥔 App governance is passed around like a hot potatoENow AppGov Score shines a light on lurking risks, providing a free App Governance Benchmark Report for your Entra tenant. Reclaim control and protect against breach & disruptions. Free upgrade to Standard Tier for 7 days once you get your score.Secure & Govern Entra Apps Now📗 Chapters 03:36 The Hackathon Origin Story 05:55 What is the Model Context Protocol? 09:22 The Token Limit Problem 15:45 Microsoft’s “Secret Sauce” Solution 19:54 Current Limitations & Future Scope 23:57 Future: Write Operations & Scripts 30:12 Security & Admin Controls 42:43 Security Copilot vs. Standalone MCP 50:21 Getting StartedPodcast Apps 🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple 📺 YouTube → https://entra.chat/youtube 📺 Spotify → https://entra.chat/spotify 🎧 Overcast → https://entra.chat/overcast 🎧 Pocketcast → https://entra.chat/pocketcast 🎧 Others → https://entra.chat/rssMerill’s socials 📺 YouTube → youtube.com/@merillx 👔 LinkedIn → linkedin.com/in/merill 🐤 Twitter → twitter.com/merill 🕺 TikTok → tiktok.com/@merillf 🦋 Bluesky → bsky.app/profile/merill.net 🐘 Mastodon → infosec.exchange/@merill 🧵 Threads → threads.net/@merillf 🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
This week, I’m joined by a stellar panel of Nathan McNulty, Ru Campbell, Martin Sandren, and Thomas Naunheim to break down the firehose of news from Microsoft Ignite related to Entra. We dive straight into the hot debate over synced passkeys versus device-bound credentials and why consumer adoption might force our hand in the enterprise. We also explore the new Account Recovery features that could save companies thousands in helpdesk costs and unpack the massive shift toward “Agentic AI” with the launch of Entra Agent ID, a feature that fundamentally changes how we think about non-human identities. If you are feeling overwhelmed by the pace of AI and identity changes, you are not alone. Listen in as we figure this out together.Subscribe with your favorite podcast player or watch on YouTube 👇About our guests* Nathan McNulty: Nathan is a Senior Security Solutions Architect at Patriot Consulting and a Microsoft Security MVP. He has been working with Microsoft cloud identity solutions since the days of Live@edu and Office 365 in 2010.* https://www.linkedin.com/in/nathanmcnulty/* Ru Campbell: Ru is a Microsoft Security MVP who leads Microsoft Security at Threatscape. He describes himself as a “jack of all trades” when it comes to Microsoft 365 security, getting involved in a wide range of security topics.* https://www.linkedin.com/in/rlcam/* Martin Sandren: Martin is the Product Lead for Identity Access at Inter IKEA, where he manages identity solutions across the globe. He offers a unique perspective as a practitioner running identity for a massive enterprise.* https://www.linkedin.com/in/martinsandren/* Thomas Naunheim: Thomas is a Cloud Security Architect at glueckkanja and a Microsoft Security MVP. He specializes in cloud security architecture and actively tracks new features and announcements in the Microsoft ecosystem.Sponsored by:Shadow IT and SaaS sprawl are outpacing IT teamsIt can feel impossible to tackle these app governance challenges:📦 Entra ID isn’t secure by default💥 SaaS adoption & sprawl isn’t slowing down⌨️ Citizen Development keeps rising (hello, Copilot Studio!)🗑️ Vendors often don’t remove apps after uninstall🔃 Offboarding is inconsistent or doesn’t happen at all🥔 App governance is passed around like a hot potatoENow AppGov Score shines a light on lurking risks, providing a free App Governance Benchmark Report for your Entra tenant. Reclaim control and protect against breach & disruptions. Free upgrade to Standard Tier for 7 days once you get your score.🔗 Related Links* Microsoft Entra: What’s New in Secure Access on the AI Frontier* Entra.Chat - Access Review Agent* Entra.Chat - Conditional Access Agent📗 Chapters00:00 Intro04:36 The Debate: Synced vs Device-Bound Passkeys20:47 Entra Account Recovery & Identity Verification30:00 Passwordless Self-Remediation33:01 Security Copilot Comes to E536:47 The Rise of AI Agents in Entra42:49 Understanding Entra Agent ID56:47 MCP Servers & VS Code Integration01:05:20 Global Secure Access & AI Security01:09:14 Microsoft Security BaselinePodcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe
This week, I’m so excited to share the inside story of a project I’ve been working on for over a year: the new Zero Trust assessment. I’m joined by some of the key folks from the team: Tarek, who’s leading the charge; Sarah and John, who are crushing docs; and Ravi, who’s owning Intune.We unpack the wild breach that sparked it all, geek out over those Sankey charts that spotlight sneaky unmanaged devices and privileged access landmines, and tease why even “expired” app creds could be your silent killer. If you’re tired of silos between identity and endpoints, this is your wake-up call—tune in to see how to make Zero Trust practical before the next attack hits.Subscribe with your favorite podcast player or watch on YouTube 👇About Our GuestsSarah LipseySarah Lipsey has been with Microsoft for almost four years and writes about monitoring and health, ID Protection, and Security Copilot in Microsoft Entra. Sarah has worked as a technical writer and instructional designer for around 20 years, and for a university, a telecommunications firm, and a railroad. She lives in the woods with her family where she loves to knit, play video games, hike, and ski. Yes, she spends way too much time trying to close out every dot on a video game map. Still working on the Skellige map for The Witcher 3.LinkedIn - https://www.linkedin.com/in/sarah-lipsey-b53b746/John FloresJohn is a Senior Content Developer at Microsoft, where he has worked for over eight years. He specializes in creating high-impact technical content for identity security within Microsoft Entra, focusing on areas like Conditional Access, MFA, ID Protection, and device identity. John also leads the documentation efforts for Zero Trust content across Microsoft 365 and Identity teams. He actively collaborates with engineers and PMs to test pre-release features and engages with customers to refine technical guidance.LinkedIn - https://www.linkedin.com/in/johnbflores/Ravi KalwaniRavi is a Senior Program Manager at Microsoft, based in Sydney, Australia. With over 14 years of IT experience spanning technical training, support, consulting, and program management, his focus for the past five years has been on Enterprise Client and Mobility, specifically Microsoft Configuration Manager and Intune. Ravi is also an experienced public speaker, having presented at numerous technical conferences and delivered a wide range of workshops for both internal teams and enterprise customers.LinkedIn - https://www.linkedin.com/in/rkalwani/Tarek DawoudTarek Dawoud is a long-time veteran at Microsoft, having been with the company for over 18 years. Tarek currently leads the architecture team within the customer engineering (CXE) organization, where he helps customers deploy Entra, gathers insights for the product group, and works to solve the hardest identity problems.LinkedIn - https://www.linkedin.com/in/tarekdawoud/🔗 Related Links* aka.ms/zerotrust/assessment → Microsoft Learn docs page for the assessment* aka.ms/zerotrust/demo → Interactive demo of a sample assessment report* aka.ms/zerotrust/feedback → Share your feedback* aka.ms/zerotrust/issues → Logging bugs & issuesZero Trust Assessment - Five minute walkthroughZero Trust Assessment ReportSample report generated by the Zero Trust Assessment tool. Try aka.ms/zerotrust/demo for an interactive demo.📗 Chapters00:00 Intro 01:11 The Origin Story: A Customer Breach 05:59 A New Way to Write Docs 08:55 Bringing Intune into the Story 11:07 How This Compares to Secure Score 14:46 Uncovering Insights with Sankey Charts 21:55 Behind the Scenes: How a Test is Built 36:18 Why We Target Privileged Access (AI Attackers) 39:59 The Myth of “Safe” Expired Credentials 42:35 Final Thoughts: “Please Run It”Podcast Apps🎙️ Entra.Chat - https://entra.chat🎧 Apple Podcast → https://entra.chat/apple📺 YouTube → https://entra.chat/youtube📺 Spotify → https://entra.chat/spotify🎧 Overcast → https://entra.chat/overcast🎧 Pocketcast → https://entra.chat/pocketcast🎧 Others → https://entra.chat/rssMerill’s socials📺 YouTube → youtube.com/@merillx👔 LinkedIn → linkedin.com/in/merill🐤 Twitter → twitter.com/merill🕺 TikTok → tiktok.com/@merillf🦋 Bluesky → bsky.app/profile/merill.net🐘 Mastodon → infosec.exchange/@merill🧵 Threads → threads.net/@merillf🤖 GitHub → github.com/merill Get full access to Entra.News - Your weekly dose of Microsoft Entra at entra.news/subscribe