Discover The Security Nexus Deep Dive
The Security Nexus Deep Dive

The Security Nexus Deep Dive
Author: The Security Nexus
Subscribed: 2Played: 8Subscribe
Share
© The Security Nexus, LLC 2025
Description
The Security Nexus is your briefing room at the intersection of cyber strategy, intelligence, and global conflict. This podcast dives deep into the ideas shaping 21st-century statecraft, where gray zone tactics, information warfare, and cyber coercion redefine the rules of engagement.
Each episode brings sharp analysis, original research, and field-tested insight from the frontlines of modern security. Whether unpacking the strategic logic behind cyber incidents or exploring decision-making failures that lead to conflict, The Security Nexus gives listeners the clarity to navigate today’s complex threat landscape.
🔗 Explore more at www.thesecuritynexus.net
34 Episodes
Reverse
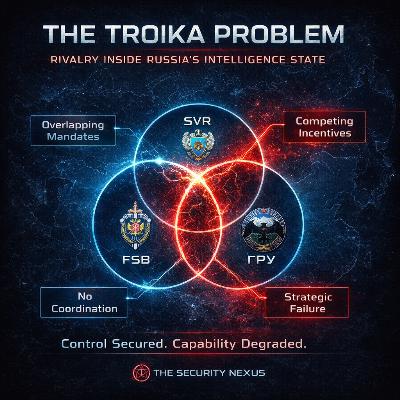
Russia’s intelligence system is built around competition, not coordination. That structure protects Putin but distorts analysis, degrades integration, and produces cascading failures. In Ukraine, those weaknesses manifested in poor strategic warning, disjointed operations, and a forced shift to tactical intelligence. Western services have recognized these dynamics but have not systematically exploited them. The Troika problem remains both a liability for Russia and an underused opportunity for its adversaries.https://www.thesecuritynexus.net
Commercial spyware has evolved into a privatized intelligence capability that allows governments to acquire advanced mobile exploitation tools without developing them internally. Platforms such as Pegasus and Predator can covertly access communications, contacts, location data, and encrypted messaging, turning smartphones into powerful intelligence collection devices. While public debate often focuses on civil liberties, the more significant issue is strategic: these tools enable adversaries to conduct intelligence operations against NATO officials, diplomats, and defense personnel through commercial intermediaries. Because the spyware market complicates attribution and bypasses traditional export controls, NATO’s current responses—primarily device-level cybersecurity measures—are insufficient. Treating commercial spyware as a collective counterintelligence threat, rather than isolated national incidents, is necessary to protect alliance decision-making networks.https://www.thesecuritynexus.net
States don’t need command authority to govern proxies—but they do need leverage. The real mechanisms are sustainment, intelligence/targeting support, sanctuary and logistics corridors, and narrative discipline. Those tools can keep proxy violence “below threshold,” but they also produce predictable failures: agency slack, autonomization, deniability collapse, and blowback.https://www.thesecuritynexus.net
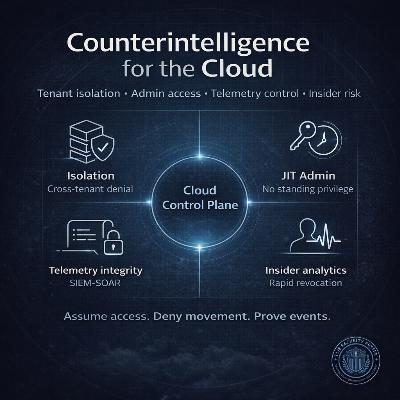
Cloud counterintelligence treats hyperscale and GovCloud environments as contested terrain. The decisive fights happen at tenant boundaries, privileged access, telemetry integrity, and insider-risk enforcement. Build for constrained privilege (JIT), durable visibility (tamper-resistant telemetry), and compartmented blast radius—then continuously verify.https://www.thesecuritynexus.net
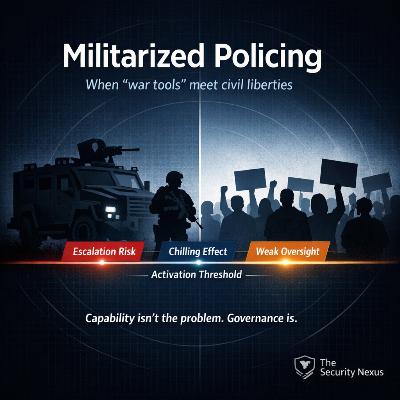
The strategic mistake is treating militarized policing as a “gear” issue. It is a governance problem: coercive capacity plus weak constraints yield predictable degradation of civil liberties. The evidence base provides little confidence that militarization systematically reduces crime or improves officer safety, while it does indicate reputational harm and potential escalation risks. A democratic state can maintain a high-end response capability, but it must make militarized deployment rare, auditable, and politically costly when misused.https://www.thesecuritynexus.net
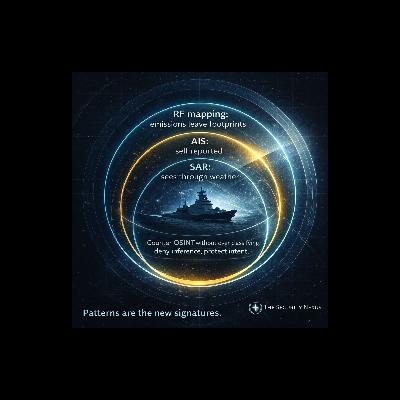
Commercial maritime sensing has made it easier to build naval order-of-battle estimates from open sources. AIS provides identity and patterns but is vulnerable to spoofing and manipulation. SAR detects ships regardless of cooperation, and fusion approaches exploit mismatches between AIS and imagery to identify anomalies and “dark ships.” Commercial RF mapping can add another layer of behavioral evidence when AIS goes silent. States should counter OSINT by reducing adversary inference through emission discipline, selective disclosure, AIS governance, and better internal sharing, rather than defaulting to overclassification.https://www.thesecuritynexus.net
International rail networks become uniquely vulnerable at borders because critical flows concentrate into a few corridors and ports of entry, while operational interdependencies (services, rolling stock, crew) turn local constraints into network wide delay cascades. The most effective countermeasures combine cross border governance (shared playbooks, joint incident command, mutual aid) with technical resilience (slack capacity, modular operations, predictive monitoring, network aware rerouting, and cyber physical hardening), all aimed at preventing constraint overload and shortening time spent in cascade mode.https://www.thesecuritynexus.net
U.S. passenger rail is an open network. Airport-style checkpoints do not scale across hundreds of stations and platforms. Effective security is layered and intelligence led: visible policing and K9 presence, randomized checks, strong reporting and intel sharing, and fast incident response and recovery. The real high-leverage work sits in the cyber-physical stack that moves trains safely: signals, interlockings, dispatch, power, and communications. The post lays out a clean threat model, clarifies federal and operator roles for “critical rail,” and closes with practical guidance for travelers as well as feasible improvements for policymakers and operators.https://www.thesecuritynexus.net
Human intelligence is not dead in the age of ubiquitous technical surveillance (UTS), but its center of gravity is shifting. In a world where phones, cars, and cities are sensors, HUMINT has to adapt around three pressure points:Sources are selected and developed in the shadow of pattern-of-life analytics, with elite targets either hyper-observable or deliberately off-grid.Covers now live or die by their digital exhaust: if your pattern looks wrong to an algorithm, your legend is already burned.Meets move from heroic “Moscow rules” streetcraft to operations that ride on, or even weaponize, the surveillance layer itself.This post extends the Security Nexus Deep Dive episode “HUMINT Adapts to Total Telemetry” and pulls the scholarly thread tighter around UTS, cyber-enabled tradecraft, and the legal/policy environment that quietly makes all of this possible.
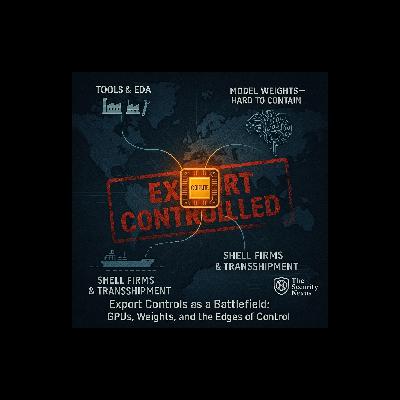
Export controls on GPUs and model weights absolutely shape the AI battlefield—but only where chokepoints are real, coalitions are tight, and enforcement data is exploited as aggressively as the hardware. Overreliance on broad, performance-based rules risks pushing adversaries toward harder-to-monitor paths and nudging the entire system toward fractured techno-blocs. A smarter architecture focuses narrowly upstream, leans into AI-enabled enforcement, and treats model weights as a special, high-friction case—not a magical lever.https://www.thesecuritynexus.net
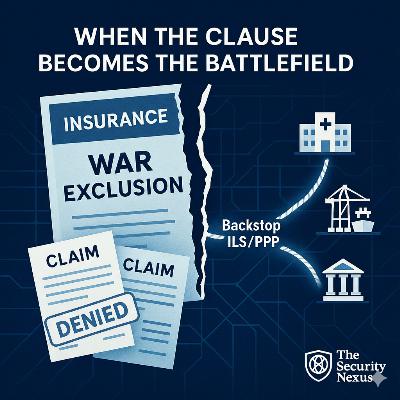
Cat-scale cyber events blow past the diversification logic that makes insurance work. As reinsurers pull back and war-exclusion language broadens, payout uncertainty grows—reshaping how boards invest, how adversaries calculate risk, and how governments contemplate backstops. The market’s fine print is fast becoming de facto cyber norms, for better or worse.https://www.thesecuritynexus.net
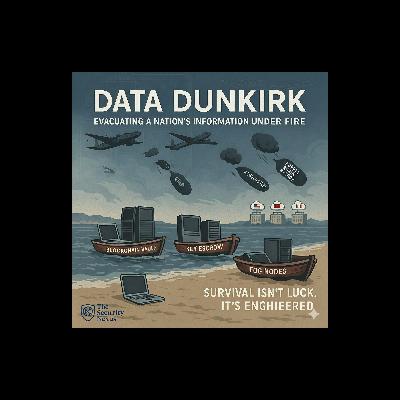
What happens when bombs — cyber or kinetic — threaten the lifeblood of a nation’s systems: its data? “Data Dunkirk” explores how modern states can preserve their most vital information assets under siege. From blockchain-enabled federated cloud systems to Cold War-era key escrow principles, this post charts an actionable blueprint for digital resilience and governance continuity. We examine decentralized backup strategies, encryption controls, and post-attack recovery architectures — because survival isn’t luck. It’s engineered.https://www.thesecuritynexus.net
Vulnerability disclosure is no longer just a technical process—it’s a diplomatic act. As cyber vulnerabilities become currency in the geopolitical marketplace, decisions about whether to patch or exploit are reshaping alliances, sowing distrust within coalitions, and forcing a reckoning with the norms of responsible state behavior. This post explores the inner workings of the U.S. Vulnerabilities Equities Process (VEP), coalition frictions over zero-day handling, and how cyber risk management choices are warping traditional diplomatic trust structures.https://www.thesecuritynexus.net
Cyber-physical power systems are increasingly vulnerable to attacks that blur the line between bits and breakers. This blog post explores how adversaries methodically move from network infiltration to catastrophic grid disruption—focusing not on abstract malware, but on the very real-world hardware where incident response must span linemen and laptops. Using recent research and the Security Nexus Deep Dive transcript, we break down the evolving kill chain, the point of no return (PNR), and how relays, substations, and the trust we place in them may be the last line of defense.https://www.thesecuritynexus.net
What happens when AI-enhanced commercial satellites, smart city sensors, retail cameras, and mobile apps converge into a single open-source intelligence stack? You get a new kind of ISR; emerging not from secret state programs, but from the fabric of daily urban life. This post examines how edge computing, multimodal remote sensing, SLAM tools, and satellite IoT are transforming situational awareness, raising new strategic dilemmas about control, ethics, and the erosion of secrecy.https://www.thesecuritynexus.net
As synthetic media becomes a tool of statecraft and subversion, deepfakes pose an acute challenge to diplomatic crisis management. This post examines emerging state and non-state playbooks for combating deception at three levels: attribution, narrative containment, and technical watermarking. From false flag videos sparking regional instability to proactive watermarking systems that could become the Geneva Conventions of digital media, this is a strategic guide for the era when seeing is no longer believing.https://www.thesecuritynexus.net
GPS is under attack. From jamming in war zones to spoofing near airports and farms, GNSS threats are rising fast. This post explores how critical infrastructure is affected and what technologies—like AI, sensor fusion, and multi-antenna arrays—are being developed to fight back. The future of navigation depends on resilience.https://www.thesecuritynexus.net
Subsea cables carry over 99% of the world's digital traffic but remain critically vulnerable to sabotage, espionage, natural disasters, and accidental damage. This post explores the triple invisibility of subsea infrastructure, highlights threats to cable security, and examines deterrence, detection, and redundancy options.thesecuritynexus.net
When regimes collapse or survive a coup, intelligence agencies face purges, realignment, or ruin. This post examines how Egypt, Turkey, and Thailand rewired their intelligence structures to maintain control—offering stark lessons in power, paranoia, and statecraft.https://www.thesecuritynexus.net#thesecuruitynexus
What began as convenience has evolved into covert capability. This deep dive explores how recommendation systems—once designed to ease cognitive load—have quietly matured into powerful intelligence actors. By collecting behavior trajectories and analyzing sentiment at scale, algorithms can now detect societal unrest, fuel disinformation, and even function as tools of modern espionage. The question isn’t just what these systems know—but how they’re being used, and by whom.https://www.thesecuritynexus.net