Discover Cyber Focus: Cybersecurity, National Security, and Critical Infrastructure
Cyber Focus: Cybersecurity, National Security, and Critical Infrastructure
Cyber Focus: Cybersecurity, National Security, and Critical Infrastructure
Author: Frank Cilluffo / McCrary Institute
Subscribed: 6Played: 93Subscribe
Share
© 2026 Cyber Focus
Description
As cyber threats evolve faster than policy, Cyber Focus delivers executive-level briefings on cybersecurity, national security, and critical infrastructure. From the McCrary Institute for Cyber and Critical Infrastructure Security at Auburn University, host Frank Cilluffo speaks with senior leaders across government, industry, and the intelligence community about ransomware, state-sponsored threats, AI, and the systems we all rely on—energy, water, telecom, and supply chains. Each episode focuses on real-world risk tradeoffs and practical steps organizations can take to strengthen resilience.
119 Episodes
Reverse
Cybersecurity now reaches far beyond government networks and traditional IT systems. In this episode, Sami Khoury explains how the threat environment increasingly touches critical infrastructure, operational technology, undersea cables, and space—and why that shift is pushing governments to work more closely with private industry and trusted international partners. Drawing on more than three decades in Canadian government, Khoury offers a clear view of how Canada has built out its cyber posture, how the Canadian Centre for Cyber Security fits into that mission, and where the threat is evolving fastest. He also reflects on the growing overlap between nation-state activity, cybercrime, and hacktivism; the promise and risk of AI; the long transition toward post-quantum security; and the enduring pull of public service in a field where the stakes keep rising. Main Topics Covered Canada's cyber strategy Critical infrastructure security OT, undersea cables, and space AI and post-quantum risk Public-private and international partnership Key Quotes: "When cyber came about or when we started paying attention to cyber, it was predominantly an IT issue. But unfortunately, these days it's not just an IT issue and we have to pay attention to OT." — Sami Khoury "We know that cyber, and it might be cliche, cyber knows no border." — Sami Khoury "We welcome people from different educational background because it's the analytical thinking capacity that we're looking for, not critical thinking skills. It's not necessarily that you're the best coder or that you are the best hardware architect. We want people with the critical thinking skills." — Sami Khoury "The day there's a cryptographically relevant quantum computer that can break today's encryption will not, I presume, will not come with a press release." — Sami Khoury "It's no longer government on government, it's government on private sector, it's mercenaries on private sector, it's mercenaries on government or hacktivist on government. So it's completely asymmetric and it takes a whole team to basically make a difference." — Sami Khoury Relevant Links and Resources Canadian Centre for Cyber Security Canada's national cyber threat assessment Canada's AI strategy Canada's Post-quantum encryption bulletin Guest Bio: Sami Khoury is the Government of Canada Senior Official for Cyber Security and the former head of the Canadian Centre for Cyber Security. He has spent over 30 years in the Canadian government, primarily within the Communications Security Establishment (CSE), Canada's signals intelligence and cryptologic agency. A veteran of the "Five Eyes" intelligence community, Khoury has been instrumental in shaping Canada's national cyber strategy and fostering deep operational ties with international partners.
Ukraine's cyber defense has become one of the clearest real-world tests of what resilience actually looks like under sustained attack. In this episode of Cyber Focus, Greg Rattray explains why Ukrainian defenders held up better than many expected, and what their experience reveals about the limits of prevention, the value of shared visibility, and the growing operational role of the private sector. Drawing on his work leading the Cyber Defense Assistance Collaborative, Rattray argues that exposing adversary activity across a more "brightly illuminated cyberspace" helped blunt Russia's offensive advantage. But the larger lesson is not just about threat visibility. It is about recovery, adaptability, and trust: teams under pressure need tools they already know how to use, leaders need to plan for bad days, and governments need to make room for industry to do more than simply wait for direction. Main Topics Covered The "bright room" concept in cyber defense Why resilience matters more than perfect prevention Familiar tools vs. cutting-edge tech in crisis The private sector's front-line role How cyber, EW, and drones are converging Key Quotes: "It's pretty hard to do cyber offense in a bright room, in a dark room, it's a lot easier. But like what we've done here is give the Ukrainians the position that the Russian attacks are trying to occur in a pretty brightly illuminated cyberspace." — Greg Rattray "Kyivstar, [Ukraine's] major telecommunications provider, got leveled in December of 2023. I thought they would be out for weeks. Two days later they were back up and running." — Greg Rattray "The speed at which drones have to change in order to stay survivable and effective; these innovation cycles are weeks, not years." — Greg Rattray "While the NIST cybersecurity framework talks about respond and recover, the amount of energy that goes into resilience is still to my mind, under thought, under exercised, [and] under invested in." — Greg Rattray "The notion that you're going to be targeted has to be part of your risk calculus. And therefore you even with a good team... you cannot guarantee you won't have a bad day." — Greg Rattray Links/Resources Cyber Defense Assistance Collaborative: https://crdfglobal-cdac.org Guest Bio: Dr. Greg Rattray is Chief Strategy and Risk Officer at Andesite and Executive Director of the Cyber Defense Assistance Collaborative (CDAC), which has facilitated more than $30 million in voluntary cyber defense support to Ukraine. He previously served as J.P. Morgan Chase's Global CISO and Head of Global Cyber Partnerships, and spent 23 years in the U.S. Air Force, including as the National Security Council's Director for Cybersecurity.
Overview Transatlantic cyber cooperation is being tested by political strain, regulatory divergence, and competing ideas about sovereignty, trust, and market access. In this episode of Cyber Focus, Sébastien Garnault argues that if the United States and Europe want to keep working together on security, they need to move quickly to make that cooperation practical, especially in critical infrastructure and digital markets. Speaking from a French private-sector perspective, Garnault makes the case that governments alone may not be able to repair or sustain that cooperation at the speed the moment requires. He points instead to private-sector partnerships, shared market incentives, and clearer language around security standards as possible ways to keep the transatlantic relationship workable even when public-sector trust is under pressure. The conversation also explores how Europe and the United States differ on clean versus trusted technology stacks, how threat perceptions shape national requirements, and how privacy, AI, and data localization debates can either strengthen or complicate cooperation. The conversation was recorded on February 11, 2026. Main Topics Covered Private-Sector Cooperation as a Strategic Bridge: Why Garnault believes business-to-business cooperation may move faster than government-to-government diplomacy when trust is strained. Clean Stack vs. Trusted Stack: How U.S. national-security thinking and EU market-standard thinking create different paths for defining who can participate in secure digital markets. Threat Perception and Market Access: How geography, history, and national priorities shape security requirements across Europe and affect access to critical infrastructure markets. Trust, Sovereignty, and the Transatlantic Reset: Why Garnault sees damaged trust as a real obstacle, and why he argues for a reset rather than a rupture in U.S.-European cyber cooperation. Privacy, AI, and Data Localization: How French and European views on privacy, regulation, and AI governance differ from those in the United States, and why those differences matter for security and interoperability. Key Quotes "Maybe what we've done in the last decade and what we will do in the next decade don't belong from government but belongs to us." — Sébastien Garnault "We can do a reset; we cannot afford a reboot." — Sébastien Garnault "The damages that have been done in our trust, mutual trust, are very deep. So we need to fix it quickly." — Sébastien Garnault "The best way for us to cooperate with our allies is to use the market because the market is less political than national security." — Sébastien Garnault "From my standpoint, the glue that binds us together is much greater than anything that can tear us apart." — Frank Cilluffo Links/Resources CyberTaskForce: https://www.cybertaskforce.fr/ Paris Cyber Summit: https://www.paris-cyber-summit.com/ Guest Bio Sébastien Garnault is the founder of the CyberTaskForce and president of the Paris Cyber Summit. He joined Cyber Focus while in Washington leading a French delegation meeting with U.S. policymakers, industry leaders, and other decision-makers, and spoke in a private-sector capacity rather than on behalf of the French government.
Electricity demand is surging—and DOE's Alex Fitzsimmons argues that the country's ability to "keep the lights on" is now inseparable from how fast we can expand energy infrastructure, how we manage affordability, and how seriously we treat security. In this conversation with Frank Cilluffo, Fitzsimmons, the Acting Under Secretary of Energy and Director of the Office of Cybersecurity, Energy Security, and Emergency Response (CESER), frames "energy dominance" as a practical governing problem: meet rapid load growth (including from AI and data centers), avoid reliability shortfalls, and do it in a way that doesn't push unacceptable costs onto everyday Americans. Main Topics Covered AI- and data center-driven demand growth Affordability and "ratepayer protection" Resource adequacy and reliability risk OT security and critical infrastructure stakes Supply chain risk and security vs speed Key Quotes "Privacy, data breaches, all of these things are important. They matter. They matter. But OT matters more. Keeping the lights on matters more." — Alex Fitzsimmons "These tech companies recognize that for their technology to be politically and economically viable, that the American people cannot be shouldered with the burden of new data centers." — Alex Fitzsimmons "We were set to lose 100 gigawatts of reliable dispatchable generation by 2030, at the same time that we may need to build 100 gigawatts of generation and associated infrastructure to win the AI race." — Alex Fitzsimmons "We have to [build supply] securely. So we can't sacrifice security for speed." — Alex Fitzsimmons "[AI-FORTS] is focused on 3 things: secure the energy system from AI, secure it with AI, and secure the AI itself." — Alex Fitzsimmons Relevant Links and Resources DOE's CESER Office DOE's Genesis Mission DOE 2025 resource adequacy report NERC; RTOs and ISOs (mentioned in the episode; link not provided) Guest Bio Alex Fitzsimmons serves in the Trump Administration as the Acting Under Secretary of Energy at the U.S. Department of Energy (DOE), where he spearheads DOE's energy dominance mission and oversees a broad portfolio of offices advancing affordable, reliable, and secure energy for the American people. He also serves as Director of DOE's Office of Cybersecurity, Energy Security, and Emergency Response (CESER), leading efforts to safeguard the nation's energy infrastructure against evolving cyber and physical threats and strengthen resilience across critical energy systems.
Cyber deterrence has long lagged behind the threat. In this special episode of Cyber Focus recorded on March 11, 2026, White House National Cyber Director Sean Cairncross argues that the United States can no longer afford a posture built mainly around resilience and response while adversaries, criminal groups, and state-backed proxies operate at low cost and low risk. He presents President Trump's new National Cyber Strategy as an effort to change that calculus by aligning government policy, offensive and defensive capabilities, industry partnership, and international coordination around a more forward-leaning approach. The conversation walks through the strategy's six pillars, from shaping adversary behavior and streamlining regulation to modernizing federal systems, securing critical infrastructure, protecting U.S. technological advantage, and expanding the cyber workforce. Cairncross emphasizes a core theme throughout: private companies should not be left to fend for themselves against foreign intelligence services and military-linked actors, and government must do more to impose cost, remove friction, and support practical security outcomes. Main Topics Covered Cyber deterrence and imposing costs on adversaries Public-private partnership and smarter regulation Federal modernization and procurement reform Critical infrastructure resilience AI, post-quantum policy, and cyber workforce development Key Quotes "Resiliency is great, but resiliency…implies that you're taking hits." — Sean Cairncross "There is a lot that can be done to deny [bad cyber actors] the benefits of their activity, to make life harder for them online and to deny them safe haven." — Sean Cairncross "I think if you get hit by a foreign adversary, for the USG to turn around and point a finger at you is essentially shifting blame… It's not going to succeed unless both sides of that coin are working together and being collaborative." — Sean Cairncross "We can work on procurement speed. We can work on technological innovation and adopting that technology much more quickly than we have." — Sean Cairncross "This [low-cost, high-reward incentive structure for malicious cyber actors] has been allowed to go too far and get too far out of whack ... and we need to reset that." — Sean Cairncross Relevant Links and Resources President Trump's National Cyber Strategy Cybercrime executive order signed the same day as the strategy Post-quantum policy / "PQC" executive order or action under development Guest Bio Sean Cairncross is the White House National Cyber Director, serving as the principal adviser to the president on cyber policy matters. Before taking this role, he served in the Trump White House as deputy assistant to the president and senior adviser to the chief of staff. He also served as CEO of the Millennium Challenge Corporation and has held senior leadership roles in politics, government, and strategic consulting.
Cyber is now woven into modern conflict, alongside conventional military force. In this episode, Frank Cilluffo examines how that shift shapes the threat from Iran—especially the risk of cyber retaliation aimed at U.S. critical infrastructure, U.S. businesses, and public confidence. Rear Admiral (Ret.) Mark Montgomery of the Foundation for Defense of Democracies brings a strategic and military lens to the discussion, explaining how cyber is being built into conflict planning alongside kinetic operations. Cynthia Kaiser, a former FBI cyber leader now with Halcyon, brings an operational view of how Iranian cyber activity can create disruption, spread fear, and produce real effects even without the sophistication of China or Russia. Main Topics Covered Cyber as an integrated warfighting tool Iran's cyber posture and likely retaliation paths Critical infrastructure and OT vulnerabilities Disruption, fear, and information effects Gaps in U.S. civilian cyber defense Key Quotes "They're not at the level of capability as Russia and China, but that's almost irrelevant. They've got a drive-by shooting capability." — Frank Cilluffo "We're seeing cyber integrated at the front end of planning. It's not cyber only or cyber as an afterthought, but it's cyber as an integrated element." — Mark Montgomery "The vast majority of our critical infrastructure doesn't have a shield."— Mark Montgomery "[Iran is] really one of the world's most malicious and capable cyber actors. They're not necessarily as good as China or Russia, but they don't need to be to have an effect." — Cynthia Kaiser "The point's the fear. The point's the chaos. And the point is the internal messaging for their own people—to say we did something in retaliation." — Cynthia Kaiser Relevant Links and Resources Foundation for Defense of Democracies Halcyon Ransomware Research Center NSA Cybersecurity Collaboration Center Guest Bio Mark Montgomery is a senior fellow at the Foundation for Defense of Democracies and former executive director of the Cyberspace Solarium Commission. He brings deep experience in cyber strategy, defense policy, and national security planning. Cynthia Kaiser is a senior cyber executive at Halcyon and a former FBI leader with extensive experience in cyber investigations and ransomware response. She brings an operational perspective on Iranian cyber activity, disruption campaigns, and cyber risk to critical infrastructure.
Cyber incident reporting is about to become mandatory for much of critical infrastructure—and the details are where the fight is. On February 26th, Frank Cilluffo spoke with Inside Cybersecurity managing editor Sara Friedman about CIRCIA's proposed reporting rules, what industry says is overbroad, and why the 72-hour clock is hard in the real world. They also dig into overlap with other federal requirements, CISA's capacity to execute the rulemaking, and what "getting it right" means for public-private trust. The conversation then pivots to NIST, AI agent standards, and how Washington is balancing innovation, security, and competitiveness. Main Topics Covered What CIRCIA is designed to do. Who's covered and what counts as reportable. The practical challenge of determining incident facts within 72 hours. Duplication concerns across rules, including SEC cyber disclosure timelines. Whether CISA has the staffing and leadership capacity to deliver. NIST's role in AI agent standards and broader cyber "rules of the road." Key Quotes "CISA was supposed to have voluntary partnerships… And with this new role, CISA is moving into more of a regulator role." —Sara Friedman "This rulemaking, when it was put out, it's over 400 pages. There's a lot in there." — Sara Friedman "House Homeland Security Chairman Andrew Garbarino threatened to, if the rulemaking does not meet congressional intent…to potentially roll this back." — Sara Friedman "When there's a large attack on critical infrastructure, it just seems to wake up lawmakers in some ways that they need to be able to do something." —Sara Friedman "They've shed about a third of their workforce…One of the questions is, does CISA have the capacity that they need for this rulemaking and to do it effectively? —Sara Friedman Relevant Links and Resources CIRCIA town halls scheduled for March: https://insidecybersecurity.com/share/17759 When the CIRCIA NPRM was published: https://insidecybersecurity.com/share/15688 RSA 2024 panel on the rulemaking: https://insidecybersecurity.com/share/15832 NIST launches AI Agent Standards initiative: https://insidecybersecurity.com/share/17775 NIST AI security request for information: https://insidecybersecurity.com/share/17654 NIST work on an AI profile for the Cybersecurity Framework: https://insidecybersecurity.com/daily-news/stakeholders-weigh-ai-considerations-cybersecurity-nist-workshop-draft-framework-profile Guest Bio Sara Friedman is the managing editor of Inside Cybersecurity and has covered federal cybersecurity policy for years, including CIRCIA, NIST standards, and related rulemakings.
Cyber threats against the Defense Industrial Base (DIB) don't stop at the battlefield—they extend into suppliers, perimeter devices, and even hiring pipelines. Luke McNamara of Google's Threat Intelligence Group joins Frank Cilluffo to unpack Mandiant's report Beyond the Battlefield: Threats to the Defense Intelligence Base and the patterns it flags across today's threat landscape. They discuss how the war in Ukraine is shaping targeting priorities, why China's cyber espionage increasingly begins at the network edge, and how "fast follower" exploit cycles compress patch timelines. McNamara also explains the North Korean IT worker problem, where remote hiring fraud can create both revenue and potential access pathways. The takeaway for mid-sized defense suppliers is practical: harden identity, reduce perimeter exposure, and assume meaningful risk often starts outside traditional corporate visibility. Main Topics Covered Why manufacturing remains a top target and a warning sign for broader supply-chain risk How the war in Ukraine is influencing cyber targeting tied to drones and UAS ecosystems China's focus on edge-device compromise (VPNs, routers, email gateways) and why it matters The "fast follower" dynamic that turns one vulnerability into many intrusions North Korean IT worker operations, remote hiring fraud, and AI-enabled deception The highest-leverage defensive priorities for DIB organizations, especially identity and MFA Key Quotes "Manufacturing is always the most targeted sector going back to 2020. And I think that's a larger canary in the coal mine." — Luke McNamara "It's not just some of these top-tier Chinese APT actors and their ability to leverage these as a zero-day, but the ability for secondary groups, once some of the details leak around a particular vulnerability, to start weaponizing it themselves." — Luke McNamara "If I had to narrow it down to one category to put more resources to, I would say identity…hardening around the identity piece is certainly key." — Luke McNamara "Organizations that are more aware of [the North Korean IT worker infiltration], where the security teams have met with their HR folks, their recruiters, helped inform them about the nature of these threats, I think they're a little bit better secured." — Luke McNamara "It sounds more like a movie than reality, but it's happening." — Frank Cilluffo Relevant Links and Resources Mandiant report — Beyond the Battlefield: Threats to the Defense Intelligence Base Mandiant podcast — Defenders Advantage Guest Bio Luke McNamara is a Deputy Chief Analyst at Google Cloud's Mandiant Intelligence and part of Google's Threat Intelligence Group, focused on cyber threat trends and emerging risks.
A new wave of cyberattacks is being routed through everyday devices—and defenders can't rely on old assumptions about geography or "known bad" infrastructure. Daniel dos Santos, VP at Vedere Labs (Forescout), walks through findings from their 2025 Threat Roundup, drawn from a global network of hundreds of honeypots and decoy systems. The conversation focuses on why web-facing systems and edge devices have become prime targets, how attackers hide inside cloud and ISP-managed networks, and what defenders can do earlier in the kill chain. Dos Santos also explains why many exploited vulnerabilities never appear on CISA's KEV list—and how security teams should think about patching and risk anyway. Main Topics How honeypots reveal attacker intent across IT, IoT, and OT environments. Why attacks increasingly come from ISP-managed networks and consumer devices. Cloud and "benign" services used to blend in and evade traditional filters. Why distributed botnets weaken country-based blocking for defenders. The rise of web-facing exploitation and the shift away from stolen passwords. Edge devices, OT exposure, and why "discovery" dominates post-breach activity. Key Quotes "We have hundreds [of honeypots] throughout the world. Some of them are simulations… Some of them are real devices… we expose them with the intention of seeing them attacked." — Daniel dos Santos "Home routers, but also home IP cameras or doorbells or solar inverters or…whatever it is that you have in your house that might be exposed to the internet and might be vulnerable can be these days recruited into a botnet." — Daniel dos Santos "Attackers…have figured out that when you find a zero-day in a popular router or a popular firewall or a popular VPN appliance, you can really go against thousands and thousands of organizations." — Daniel dos Santos "With one zero-day or one critical exploit, you can compromise thousands of organizations today." — Daniel dos Santos "But what we do see in the signals that we see there and what we present in the report is that there is a whole world of vulnerabilities being exploited." — Daniel dos Santos Relevant Links and Resources https://www.forescout.com/research-labs/2025-threat-roundup/ https://www.forescout.com/blog/anatomy-of-a-hacktivist-attack-russian-aligned-group-targets-otics/ About the Guest: Daniel dos Santos is the VP of Research at Forescout Research — Vedere Labs, where he leads a team of researchers that identifies new vulnerabilities and monitors active threats. He holds a PhD in computer science, has published over 35 peer-reviewed papers, has found or disclosed hundreds of CVEs — and is a frequent speaker at security conferences.
Grid resilience has become a test of whether the U.S. can keep essential systems running through disruption—and recover fast when they don't. In this episode, Frank Cilluffo talks with Scott Aaronson about how the electric power sector plans for and responds to an "all-hazards" landscape, from major storms to cyber and physical attacks. Aaronson explains why the grid is a "network of networks" with a huge attack surface but few true single points of failure, and how mutual assistance became a national-scale capability. They also dig into interdependencies across "lifeline" sectors, the practical reality of IT/OT differences, and why surging demand—from AI and data centers to EVs and reshoring—raises urgent reliability and supply chain questions. Main Topics Covered Why electricity is consumed the moment it's produced—and why balance matters. How mutual assistance evolved from bilateral help to national-scale response. Lessons from severe weather events, including what makes ice storms uniquely hard. The IT vs. OT gap, and why operational tech changes the cyber playbook. Interdependencies: why adversaries can hit electricity by targeting other sectors. Rising demand and the push to rebuild domestic manufacturing capacity for grid equipment. Key Quotes "Electricity is the only commodity that is consumed at the moment it is produced." – Scott Aaronson "[Power companies] are competitive in some ways, but we are completely non-competitive when it comes to security, when it comes to resilience, when it comes to response and recovery." – Scott Aaronson "I don't really care if it is a storm or a pandemic or a cyber or physical attack or the zombie apocalypse… The impact is what matters." – Scott Aaronson "The adversary is not attacking the electric sector. They are attacking the United States." – Scott Aaronson "The first 72 are on you… Have food, have water, have a plan, be prepared. The cavalry is coming." – Scott Aaronson "Regulations are great, but they are a foundational level of security… if you mandate… a 10-foot fence… the adversary brings a 12-foot ladder." – Scott Aaronson Relevant Links and Resources Edison Electric Institute (EEI) Electricity Subsector Coordinating Council (ESCC) CRISP (Cyber Risk Information Sharing Program) STEP (Spare Transformer Equipment Program) ESF-12 (Emergency Support Function 12 – Energy) About the Guest Scott Aaronson is Senior Vice President for Energy Security and Industry Operations at Edison Electric Institute (EEI) and Secretary of the Electricity Subsector Coordinating Council (ESCC), serving as a key industry-government liaison on power-sector security and preparedness.
Supply chains are essential infrastructure—and the iPhone's supply chain sits at the center of U.S.–China competition. As Washington reassesses economic security, this episode explores what it looks like when market incentives collide with geopolitical reality. Frank Cilluffo speaks with Patrick McGee, author of Apple in China, about his reporting on Apple's deep manufacturing reliance on China—and what that reveals about leverage, resilience, and risk. They explore how industrial capacity is built through repetition, why diversification is harder than headlines suggest, and how concentrated production creates choke points that can ripple far beyond consumer tech. The result is a clear, practical case study in why supply chains matter for critical infrastructure, national security, and long-term competition. Main Topics Covered How "learning by doing" powered China's rise in high-end electronics manufacturing The "epic transfer of technology" behind Apple's scale and China's supply-chain competence Xi Jinping's post-2013 pressure campaign and Apple's strategic recalibration in China Why supply-chain diversification is slower than headlines suggest, especially in India The "red supply chain" and how Apple suppliers became capability multipliers Taiwan/TSMC as a single-point-of-failure risk—and the AI chip-export debate it echoes Key Quotes "China isn't dependent on Apple in the way that Apple is inarguably dependent on China. My big worry in a certain sense is that the student has become the master." — Patrick McGee "If you just take the $55 billion that they invested in 2015 alone, which was 22% of revenue … and just go from let's say the birth of the iPhone 2007–2025, you're talking about a trillion dollars that Apple's invested in China." — Patrick McGee "None of those phones are really being made in India, they're just being assembled there. The joke that one manufacturing design engineer told me was that the phones are assembled in China, disassembled in China and sent to India for reassembly." — Patrick McGee "Our narrative is essentially that Apple exploits Chinese workers. In a certain sense, that's the only narrative about Apple in China we've had in the past two decades. And I flip that on its head…[China is] getting more out of the relationship. It's a story about China exploiting Apple. — Patrick McGee "I think there still is a mindset that China is an imitator, not an innovator. I think we should recognize that… is not the case." — Frank Cilluffo Relevant Links and Resources Apple in China (Patrick McGee's book) McCrary Institute' Code Red report on "Typhoon" threat actors (Vault/Salt/Flax) Anthropic's Dario Amodei's essay: "The Adolescence of Technology" Guest Bio Patrick McGee is a Financial Times journalist and the author of Apple in China, covering geopolitics, technology, and global supply chains.
Madison Horn joins host Frank Cilluffo to explain why AI-driven cyber risk may be quieter, faster, and harder to spot in 2026. She breaks down "cascading failures" in critical infrastructure—and how a disruption in one sector can quickly ripple into others. The conversation zeroes in on AI agents, especially their ability to create new user accounts, get access to systems, and hide inside everyday routine activity. Horn also warns that AI supply chain weaknesses could spread faster than traditional zero-days. Main Topics Covered Why AI-enabled attacks may look like normal business activity. Cascading failures across water, power, telecom, and healthcare systems. AI agents creating identities and operating with "human-like" access. Why "AI supply chain" risk could eclipse zero-day exploits. "Slow and steady" AI adoption for critical infrastructure operators. Why quantum planning should happen alongside today's AI rollouts. Key Quotes "Within critical infrastructure… water needs electricity, electricity needs telcos, and healthcare needs all three." —Madison Horn "Hackers are lazy. And I mean that not to be offensive, but if you can reach your objective, reaching the lowest hanging fruit, then you're going to." —Madison Horn "Attacks are not going to look as restricting and as loud. I think it's going to look just like business as normal until we see [impacts] in the physical world." — Madison Horn "What I worry about is people assuming and trusting that an AI tool is doing what it's supposed to and not necessarily understanding or being able to detect that it's doing something malicious." — Madison Horn "I just don't want quantum to get lost into the AI conversation." — Madison Horn Relevant Links and Resources Madison Horn's 2026 predictions (Nextgov) About the Guest Madison Horn is the national security and critical infrastructure chief advisor at World Wide Technology, with 15+ years leading cyber strategy and incident response in high-consequence, regulated environments. She previously held senior roles at Siemens Energy, PwC, and Accenture Security, and founded Roserock Advisory Group focused on cybersecurity and geopolitics.
CISA leadership, NSA/Cyber Command staffing, and offensive cyber operations are colliding early in 2026. Frank Cilluffo and reporter David DiMolfetta unpack Sean Plankey's renomination for CISA Director, and what a prolonged leadership vacuum can mean for agency direction and momentum. They then turn to Lt. Gen. Rudd's confirmation hearing and the evolving debate over the Title 10/Title 50 "dual hat." The conversation also examines morale and workforce pressures inside NSA, including reported staffing reductions. It closes with "Absolute Resolve," what public discussion of cyber "effects" might signal for deterrence, and a China-linked House staff email breach that frames what Molfetta is watching next. Main Topics Covered What Sean Plankey's CISA renomination signals about cyber leadership priorities. Why "core mission" talk at CISA still depends on who's in charge. Lt. Gen. Rudd's hearing, and how the dual-hat debate is evolving. NSA morale and workforce cuts, and what that means for capability. "Absolute Resolve," cyber effects, and the deterrence value of public signaling. House staff email targeting, Salt Typhoon questions, and the midterms-AI threat mix. Key Quotes "Cisa's work does not stop. That said, if you don't have a permanent leader in place, you don't have a guy to set direction, and things can't really go anywhere." — David DiMolfetta "When you don't have people at their desks [because of workforce reductions], that means they may not be tracking adversaries, they may not be doing that work to cultivate relationships with sources on a kind of human intelligence style level. — David DiMolfetta "[In Venezuela] lights went off, but they also went back on." — David DiMolfetta "Authority, accountability, and resources — I found those to be the three criteria to get things done in D.C." — Frank Cilluffo Relevant Links and Resources David DiMolfetta's stories at Nextgov.com Guest Bio: David DiMolfetta covers cybersecurity for Nextgov. Previously, he researched The Cybersecurity 202 and The Technology 202 newsletters at The Washington Post and covered AI, cybersecurity and technology policy for S&P Global Market Intelligence. He holds a BBA from The George Washington University and an MS from Georgetown University.
Chris Inglis joins Frank Cilluffo to break down what offensive cyber strategy should look like in an era of strategic competition. Drawing from the McCrary Institute's new report on U.S. cyber policy, Inglis argues that resilience and consequences are not competing theories—they have to work together. He explains why "defend forward" and persistent engagement reshaped authorities and expectations after 2018, including how NSPM-13 changed delegation for operations. The conversation also tackles the messy seam between Title 10 and Title 50 in cyberspace, and why integration—not exquisite tools—will decide whether cyber power is truly strategic. Main Topics Covered Why offense and resilience must operate as one integrated cyber strategy Cyber deterrence as changing an adversary's decision calculus, not perfection How NSPM-13 helped shift delegation and operational tempo in 2018 What "defend forward" means in plain terms—and why it's defensive Blurring of Title 10 and Title 50 in cyberspace—and why that matters The warning: the U.S. is behind on integrating cyber with power Key Quotes "My view is that the discussion of whether it's going to be a focus on defense kind of inherent resilience or a focus on imposing consequences is a false choice." — Chris Inglis "But when you get to cyberspace, it turns out that the Title 50, which is trying to get information from cyberspace, and the Title 10, which is trying to actually achieve effects in cyberspace, are about 90% the same." — Chris Inglis "[With defend forward] We're not going to wait onshore for [malicious cyber activity] to arrive and then kind of cede the initiative to adversaries." — Chris Inglis "What keeps me awake at night? We don't have time. We're way behind the curve." — Chris Inglis Relevant Links and Resources McCrary Institute report — U.S. Cyber Policy: Offense, Deterrence, and Strategic Competition Guest Bio Chris Inglis is the former U.S. National Cyber Director and former NSA Deputy Director, with decades of experience in national security and cyber policy.
Cyber Focus kicks off 2026 (and its 100th new episode) with rapid-fire predictions from McCrary Institute senior fellows. They flag big policy inflection points—especially whether Congress can reauthorize "CISA 2015," sustain information-sharing protections, and keep state and local cybersecurity funding on track. Tech-wise, the group focuses on AI's accelerating integration, the "speed" divide between defenders and adversaries, and emerging pressures across connectivity and infrastructure. On threats, they warn about deepfake-driven social engineering, ransomware that's getting faster and more accessible, "typhoon" intrusions, and the compounding risk of encryption and security tech debt. Main Topics Covered CISA 2015 reauthorization, information sharing, and state/local cyber funding priorities. Cyber offense and deterrence: shaping adversary behavior by imposing real costs. AI everywhere: faster attacks, faster defense, and higher infrastructure stakes. Convergence and connectivity: data centers, wireless, subsea cables, satellite, and scale. Deepfake social engineering and shrinking ransomware dwell times in 2026. "Typhoon" intrusions, critical infrastructure exposure, and major-event targeting pressure. Key Quotes "What I believe is going to overtake identity just in general is deep fake social engineering. And that means the calls that look like your CEO that tell you to get on an urgent call right now... I think I'd click on that if I didn't know better. And a lot of us in the security realm would." — Cynthia Kaiser "We're actually getting the broader dividing line between haves and have nots... If you can't move fast, you're going to need to find someone who can... If you're someone that can't receive new information and immediately improve your defensive posture, you're probably a have not." — Matt Hayden "We're seeing and hearing that the US government is interested in taking the fight to the adversaries... shaping the adversary's behavior is important because it slows them down, it imposes costs on them, and perhaps it could lead to deterrence." — Christopher Roberti "I started with China and I'm going to end with China... making sure again, we don't take our eye off the ball that wow, there may be reasons to make deals economically with China. We have to treat them as a potential adversary." — Bob Kolasky "At the end of the day, I look at as the typhoon epidemic—Salt, Vault... What is the next typhoon we're going to uncover in 2026 that's going to be driving our cybersecurity defense measures?" — Bill Evanina Relevant Links and Resources https://mccraryinstitute.com/directory/senior-fellows/
AI is speeding up cyber operations and shrinking the window for defenders to respond. Nick Andersen, who leads CISA's Cybersecurity Division, explains why Anthropic's recent report caught attention: it described what Anthropic called the first publicly reported AI-orchestrated cyber espionage campaign, in which threat actors misused its Claude models to automate and scale parts of an intrusion. Andersen and Frank Cilluffo unpack what that signal means for resilience, from model safeguards to the infrastructure and people surrounding them. They apply secure-by-design thinking to frontier AI, stress risk ownership for adopters—especially in OT—and warn against silver-bullet claims. The conversation closes on what it takes to build capacity, including KEV-driven prioritization and CISA's Scholarship for Service pipeline. Main Topics Covered Why AI changes cyber defense through speed, scale, and attacker efficiency. What the "Anthropic/Claude" case signals about resilience for AI providers. Secure-by-design expectations for AI systems and the infrastructure around them. OT adoption: governance, data flows, and safety-first decision-making. Workforce and talent pipelines, including CISA's Scholarship for Service interns. Practical prioritization: vulnerabilities, KEV, and remediation at operational pace. Key Quotes: "If we don't engage now in having a resilience conversation around our artificial intelligence companies, we're going to see a lot more of what, what happened with Claude, in this case." – Nick Andersen "The core principles regarding what we're focused on as cyber defenders don't necessarily change here, but the speed through which I think we can expect known vulnerabilities to be weaponized and exploited in the wild now that's going to change for us." – Nick Andersen "There is no silver bullet. Anybody who has a sales pitch they're receiving that says that this AI solution is going to solve all of your problems... they should immediately become exceedingly skeptical and start asking an awful lot of questions." – Nick Andersen "OT operators are going to have some really tough conversations coming up about what control are they willing to give away... We know within the OT environment safety and security has to come first." – Nick Andersen "Our adversary has a pretty clear-eyed view of what they're trying to achieve. And it is both the opportunities for, you know, discord and societal panic." – Nick Andersen Relevant Links and Resources House Hearing: The Quantum, AI, and Cloud Landscape: Examining Opportunities, Vulnerabilities, and the Future of Cybersecurity Anthropic Report: Disrupting the first reported AI-orchestrated cyber espionage campaign CISA: Principles for the Secure Integration of Artificial Intelligence in Operational Technology CISA: Scholarship for Service Guest Bio: Nick Andersen serves as Executive Assistant Director for CISA's Cybersecurity Division, where he leads national efforts to defend against major cyber threats and improve the resilience of U.S. critical infrastructure. He previously held senior cyber leadership roles at the White House, the Department of Energy, and in intelligence roles for the Coast Guard and Navy.
In this re-releases episode of Cyber Focus, host Frank Cilluffo sits down with Admiral Mike Rogers (Ret.), former Commander of U.S. Cyber Command and Director of the National Security Agency. Rogers shares insights from his leadership across two administrations, discussing offensive cyber operations, the evolution of Cyber Command, and pressing national security challenges. The conversation spans from undersea cable vulnerabilities to public-private integration, the future of quantum and AI, and the enduring need for clarity in cyber policy. A decorated Auburn alum, Rogers reflects on lessons learned, historical inflection points, and what must change for the U.S. to stay ahead in the cyber domain. Main Topics Covered: Shifting to a proactive cyber posture: persistent engagement and defend forward The evolving role of Cyber Command and comparisons to SOCOM Vulnerabilities in undersea cable infrastructure and space-like situational awareness Lessons from Ukraine on real-time public-private integration Strategic implications of AI and quantum technologies Key Quotes: "I believe that what [offensive cyber actions] we ought to authorize is not just going after infrastructure but directly going after capability within those nations that are generating these effects against us." — Adm. Mike Rogers "If you're going to deter an entity, they have to have some level of awareness of both [your] capability and intent." — Adm. Mike Rogers "If you had asked me five years ago when I left Cyber Command, would a foreign entity, in this case a nation-state, upload destructive malware into critical U.S. infrastructure in a time of peace?... I would have said to you… there's a low probability. Boy, I got that wrong." — Adm. Mike Rogers "I think it requires a little precision in how we discuss these matters. Because not all hacks are the same, not all hackers are the same, not all intentions are the same, not all capabilities are the same. [Not] everything is an 'attack'." — Frank Cilluffo "I'm not interested in collaboration; I'm interested in integration. I'm interested in a real-time situational awareness between government and the private sector." — Adm. Mike Rogers Relevant Links and Resources: U.S. Cyber Command – Mission and Vision https://www.cybercom.mil/About/Mission-and-Vision/ NSA – About the Agency https://www.nsa.gov/about/ Cyberspace Solarium Commission Final Report https://www.solarium.gov/report Guest Bio: Adm. Mike Rogers (Ret.) served as the Director of the National Security Agency and Commander of U.S. Cyber Command from 2014 to 2018. A four-star admiral with a distinguished 37-year career in the U.S. Navy, he helped shape modern cyber strategy at the highest levels of government. Since retiring from active duty, he has advised Fortune 500 companies, startups, and global institutions on cyber, intelligence, and national security issues.
Undersea cables quietly carry almost all global internet traffic yet rarely feature in security debates. This episode explains how subsea infrastructure underpins the global economy, data flows, and modern military operations while facing frequent "accidental" disruptions and growing geopolitical risk. Listeners hear why chokepoints, island dependencies, and hotspots from the Red Sea to the Taiwan Strait keep national security officials up at night. The conversation also explores how redundancy, smarter investigations, and faster permitting can harden this hidden backbone against both negligence and sabotage. Frank and Alex close by looking at AI, quantum, fiber sensing, and satellite backups as the next frontier for cable resilience and deterrence. Main Topics Covered Subsea cables as the physical backbone of global internet and finance. How outages happen, from ship anchors to suspected sabotage. Strategic chokepoints, island dependencies, and contested regions like the Red Sea. Building resilience through redundancy, permitting reform, and trusted infrastructure partners. New monitoring tools: fiber sensing, AI, and quantum for cable security. How governments and industry share intelligence and fund resilient capacity. Key Quotes: "Subsea cables carry the vast majority of Internet traffic around the world… Estimates vary from 95 to 99% of Intercontinental data traffic. So when you think about the Internet, subsea cables are the basis of the Internet." "Redundancy is our biggest defense… We have 100 cables coming into the US and therefore it makes it very hard to do anything meaningful in a short time frame to actually impact it. "Do I think our adversaries would want to do this [tap cables]? Yes... Do I think they can do it? Possibly. Do I think the juice is worth the squeeze? No, I don't." "There were more cable cuts in the Taiwan Strait in January of this year than either 2024 or 2023 in total. That is a sharp uplift at a time when we know that hostility in that part of the world is rising. I would be shocked if none of those incidents were knowingly done." "The entire Starlink... global capacity is equivalent to [only a few] subsea cable[s]... So when you talk about truly replacing [subsea cables], it's not there." Relevant Links and Resources Alex Botting paper "Shoring Up Subsea Security" for the Center for Cybersecurity Policy and Law. House Homeland Committee Hearing: An Examination of Foreign Adversary Threats to Subsea Cable Infrastructure Alex's Podcast: Distilling Cyber Policy Guest Bio: Alex Botting is the Senior Director of Global Security & Technology Strategy at Venable. His career has focused on shaping policies at the intersection of security, technology & telecoms in more than 50 countries and multilateral organizations around the world. In November he testified before the House Homeland Security Committee about threats to the subsea cable infrastructure.
Army Principal Cyber Advisor Brandon Pugh joins Frank Cilluffo to address a stark reality: if critical infrastructure fails, the Army cannot mobilize. To meet this "no fail" mission, Pugh explains how the service is aggressively merging cyber with electronic warfare and cutting red tape to field new technology in days rather than years. They also discuss the Army's unique edge in this digital fight—Reservists who bring high-level private sector expertise directly to the battlefield. The conversation also explores how AI and operational technology are reshaping the Army's cyber battlefield and threat landscape. Main Topics Covered • How Congress created the principal cyber advisor role and defined its authorities. • Army cyber's four focus areas: AI, defense critical infrastructure, acquisition, and workforce. • Integrating cyber, electronic warfare, RF, and information operations into Army warfighting doctrine. • Defending defense critical infrastructure and preparing for Volt Typhoon-style cyber disruptions. • Leveraging AI for continuous monitoring, faster detection, and protection of sensitive Army data. • Reforming cyber acquisition through FUZE prototypes, VC-style partnerships, and Guard and Reserve expertise. Key Quotes "Cyber is not an isolated capability. It's not something that just rests at Fort Gordon or Fort Meade." – Brandon Pugh "If an adversary goes after one of our military bases and we can't mobilize people, tanks, equipment in a time of conflict, that is a major concern… we can't accept the fact that cyber could be the barrier to our ability to do other military tasks." – Brandon Pugh "It's a national security imperative to leverage AI. We know adversaries are going to leverage AI or exploit our AI regardless of what we do here. We could put barriers in terms of aggressive regulation which some have proposed in the past or seek to slow it down. All that's going to do is help our adversaries." – Brandon Pugh "We have some individuals that show up their reserve weekend in $300,000-$400,000 vehicles because they are the experts in what they do as civilians. They have signed up and taken the oath because they want to serve this country. That is the talent we have in the Reserve and Guard that we need to continue to expand." – Brandon Pugh "We don't have to go through a multi-year acquisition cycle, spend millions of dollars where we've seen 3D printed drones for mere dollars in some cases being leveraged [in Ukraine]… We need some of these capabilities in a matter of days or weeks, not years." – Brandon Pugh Relevant Links and Resources • Jack Voltaic: Critical infrastructure resiliency • Army's FUZE Initiative Guest Bio Brandon Pugh is the Principal Cyber Advisor to the Secretary of the Army, advising the Secretary and Army Chief of Staff on cyber readiness, budget, capabilities, and strategy. He previously served as a director at the R Street Institute and continues to serve in the U.S. Army Reserve as a national security law professor, having earlier been a paratrooper and international law officer.
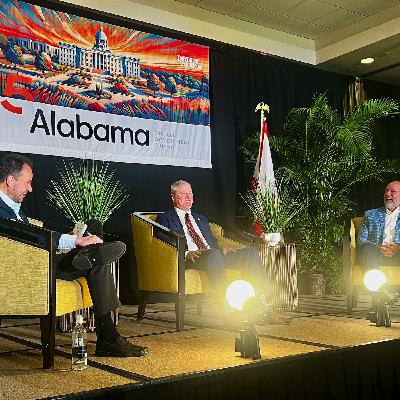
State and local governments are stepping up to defend critical services against fast-evolving cyber threats. In this episode of Cyber Focus, Alabama's top IT leaders show how they're staying ahead of the curve. They explain how a hybrid, highly decentralized environment forces them to lean on shared standards, SLCGP funding, and whole-of-state partnerships. Along the way, they unpack a recent incident that came dangerously close to crisis and what it revealed about tools, visibility, and trust. They also look ahead to AI-enabled attacks, deepfakes, and "distortion," and why automation and better intel will shape Alabama's next moves. Watch to see what other states, utilities, and local leaders can learn from Alabama's playbook. Main Topics: How Alabama OIT governs technology across roughly 140 executive agencies in a mostly decentralized environment. Using SLCGP funds, shared contracts, and enterprise tools to lift up smaller municipalities that lack resources. Rethinking threat intelligence by pairing MS-ISAC and CISA feeds with deep knowledge of state business processes. Lessons from a major cyber incident, including incident-response retainers, tooling gaps, and the value of open communication. Building whole-of-state partnerships with CISA, FBI, utilities, National Guard, and the McCrary Institute through exercises and real incidents. Preparing for AI-enabled cyberattacks through automation, platform integration, and continuous upskilling for Alabama's cyber workforce. Key Quotes: "Cybersecurity is a team sport. It's not just one person. We're trying to build the community." — Daniel Urquhart "There's a huge concern that I have as we think about the amount of threats that are going to come at us from an AI enabled cyber attack. It is going to be so broad and so unlike anything that we've seen today." — Chad Smith "I think we have to be willing to talk about [a recent cyber incident] so that people can learn from it, but also so that people know, hey, they're actually doing something and things are happening in a way that we can respect."— Chad Smith "We try to do a lot of education and team building and building that cohesive whole estate approach by setting up technology demos and articulating the why." — Daniel Urquhart "We've done a really good job the last couple of years working with the FBI, Secret Service, National Guard. Those types of partnerships can make us stronger as a state." — Daniel Urquhart Relevant Links and Resources · Alabama Office of Information Technology · Multi-State Information Sharing and Analysis Center Guest Bios: Daniel Urquhart is the Secretary of the Alabama Office of Information Technology. OIT is responsible for the strategic planning, governance, and resource utilization of all IT for the State of Alabama. Before joining OIT, he served as CIO for the Alabama Law Enforcement Agency, where he worked with industry partners to build a state-of-the-art criminal justice network. Chadwick Smith serves as the Chief Information Security Officer for Alabama's Office of Information Technology (OIT). Mr. Smith has worked in the technology industry for over twenty-five years. Prior to joining OIT, Chad worked in the insurance, banking, and data communications industries.