Securing Java Microservices with Zero Trust Architecture
Description
This story was originally published on HackerNoon at: https://hackernoon.com/securing-java-microservices-with-zero-trust-architecture.
Zero Trust replaces outdated network trust in microservices. Learn how identity, mTLS, OPA, and Vault build a secure, modern architecture.
Check more stories related to cybersecurity at: https://hackernoon.com/c/cybersecurity.
You can also check exclusive content about #zero-trust-security, #cloud-security, #microservices-architecture, #api-key-leak-risks, #mtls-authentication, #hashicorp-vault-secrets, #opa-authorization, #identity-based-security, and more.
This story was written by: @damodharapalavali85. Learn more about this writer by checking @damodharapalavali85's about page,
and for more stories, please visit hackernoon.com.
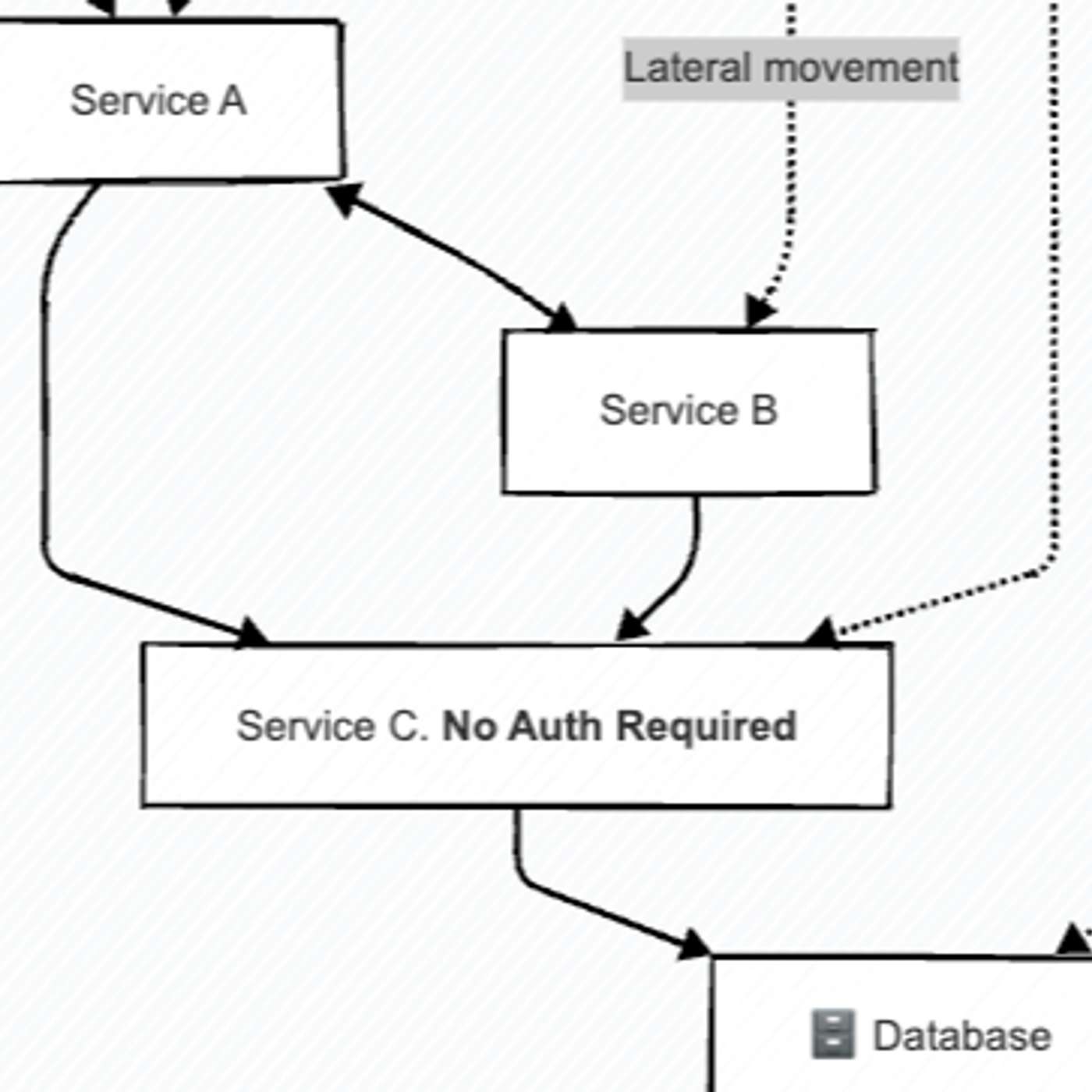
Microservices still rely on outdated “implicit trust” models that make leaked API keys catastrophic. This article explains how Zero Trust—built on identity, mTLS, OPA, and dynamic secrets—redefines secure service-to-service communication and shows how to implement it in Java and Spring Boot.